0.0 Executive Summary
This report documents the implementation and analysis of granular privilege escalation using the sudoers framework in an Ubuntu Server environment. The objective was to configure specific user privileges that allowed cross-user script execution without password prompts. This project focused on utilizing the NOPASSWD directive to enable automation while maintaining the Principle of Least Privilege (PoLP).
The result was a validated, noninteractive execution path, where a restricted user could execute a specific script as another target user. This reduces the need for manual authentication and restricts execution to a controlled command path.
1.0 Sudoers Privilege Escalation
1.1 Project Description
The goal of this task was to develop proficiency in managing advanced Linux permissions and automating cross-user tasks without compromising the system security.
The implementation utilized the /etc/sudoers configuration to
- Define specific execution rights for individual users
- Implement passwordless execution for targeted binaries and scripts
- Enforce cross-user context switching (e.g., user1 executing as user2)
- Validate security enforcement through non-interactive command testing
This workflow demonstrates how system administrators can enable secure automated processes by scoping elevated privileges to specific verified scripts.
1.2 Technical Task / Troubleshooting Process
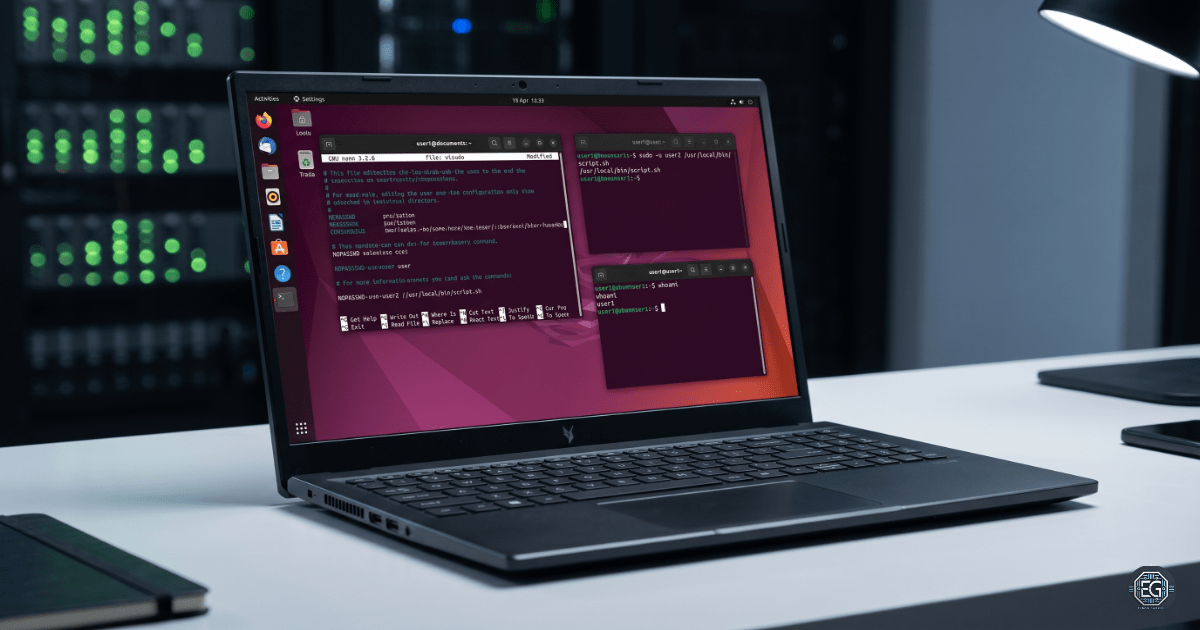
The process focused on utilizing the visudo utility to modify the system’s authorization policy with precise syntax.
Key Actions and Observations
- User and Resource Preparation
- Created two restricted accounts (
user1anduser2) to test privilege boundaries - Developed a shell script (
/usr/local/bin/hello.sh) owned by the target user - Applied restricted permissions (
700) to ensure only authorized execution
- Created two restricted accounts (
- Sudoers Policy Implementation
- Used
sudo visudoto safely edit the configuration with syntax validation - Added a scoped rule:
user1 ALL=(user2) NOPASSWD: /usr/local/bin/hello.sh - Enabled
user1to execute the script asuser2without a password
- Used
- Privilege Validation
- Executed:
sudo -u user2 /usr/local/bin/hello.sh - Used
whoamiwithin the script to confirm execution context asuser2
- Executed:
Troubleshooting Highlights
- Syntax Sensitivity
- Identified that
sudoersrules are highly sensitive to formatting and order - Prevented misconfiguration by using
visudo, which blocks invalid syntax
- Identified that
- Permission Denied Errors
- Encountered execution failures due to strict file permissions (
700) - Resolved by ensuring correct user context (
-u user2) matched the defined policy
- Encountered execution failures due to strict file permissions (
1.3 Resolution and Validation
The configuration was validated by testing the noninteractive execution path and verifying the identity context.
| Parameter | Configuration Value |
|---|---|
| Primary Tool | Sudoers Framework (visudo) |
| Privilege Type | NOPASSWD Implementation |
| Execution Path | /usr/local/bin/hello.sh |
| Scope | Controlled Cross-User Execution |
Validation Steps
- Passwordless Verification
- Confirmed that
user1could execute the script without a password prompt
- Confirmed that
- Context Verification
- Verified execution context using
whoami, confirming execution asuser2
- Verified execution context using
- Policy Scope Proof
- Attempted to run other commands using
sudo - Confirmed that access was denied or required a password
- Attempted to run other commands using
- Negative Testing
- Verified that unauthorized commands outside the defined rule were not permitted
2.0 CONCLUSION
2.1 Key Takeaways
- Granular Control: The
sudoersfile enables precise control over command execution and user context - Automation Support:
NOPASSWDallows non-interactive execution for scripts and services - Configuration Safety:
visudoprevents syntax errors that can break administrative access - Least Privilege: Restricting access to specific scripts reduces the attack surface
2.2 Security Implications and Recommendations
Risk: Script Modification (Privilege Escalation)
If a script defined in the sudoers file is modified by unauthorized users, it can be used to execute malicious commands with elevated privileges.
Mitigation
- Enforce strict ownership (
rootor target user) - Apply secure permissions (
700or755) - Store scripts in protected directories such as
/usr/local/bin
Risk: Stale Privilege Entries
Unused or outdated NOPASSWD rules may create hidden access paths.
Mitigation
- Regularly audit
/etc/sudoersand/etc/sudoers.d/ - Remove entries tied to unused users or deprecated scripts
Best Practices
- Always use
visudofor editing privilege configurations - Define rules using absolute paths to prevent abuse
- Limit
NOPASSWDusage to only required commands - Combine privilege rules with strict filesystem permissions
- Document all changes for auditing and compliance tracking
Framework Alignment
- NIST SP 800-53 (AC-6): Enforcement of Least Privilege
- CIS Control 5: Account and privilege management
- PCI-DSS / SOC 2: Controlled and auditable access mechanisms