System Administration & Infrastructure Operations
Building, Securing, and Troubleshooting Real-World Systems
Infrastructure Operations Portfolio
This portfolio demonstrates hands-on systems administration, infrastructure security, and operational troubleshooting in Windows and Linux environments. Projects focus on server hardening, monitoring deployment, backup and recovery operations, network security, and technical problem resolution using structured validation and root-cause analysis methods.
Each project follows a proof-of-work approach, where infrastructure concepts are tested through practical implementation, troubleshooting, documentation, and security validation aligned with industry frameworks and operational best practices.
Focused on operational reliability, infrastructure security, monitoring visibility, and structured troubleshooting across enterprise-style lab environments.
Available Infrastructure Services
Systems Administration
- Windows Server admin
- Linux administration
- User & permissions
- Service troubleshooting
- System monitoring
- Operational support
Infrastructure Hardening
- GPO hardening
- Linux security baselines
- Least privilege access
- Registry restrictions
- RDP/SMB hardening
- Firewall rules
Monitoring & Logging
- SAR metrics
- Event log analysis
- Process monitoring
- Log filtering (grep)
- Resource tracking
- Performance diagnostics
Network Defense
- pfSense firewalling
- Traffic control
- VPN setup
- DNS/routing checks
- Segmentation
- Network fixes
Backup & Recovery
- Backup validation
- Snapshots
- Restores
- DR planning
- System recovery
- Continuity support
Security Governance
- NIST-aligned controls
- Risk validation
- Security mapping
- Audits
- Documentation
- Incident support
Explore Technical Portfolio View Certifications
Professional Influence
George H. Ross
NBC’s ‘The Apprentice’ Judge & Mentor
Reinforced structured decision-making, operational discipline, and risk evaluation principles used when analyzing infrastructure issues, system reliability, and security controls.
Wahida Clark
4x NYT Bestselling Author
Strengthened professional communication and documentation skills used to translate technical findings, operational risks, and troubleshooting outcomes into clear, business-focused reports.
Stedman Graham
Author, Educator & Business Strategist
Participated in a professional virtual engagement focused on leadership, personal development, and strategic thinking skills. The discussion reinforced structured goal-setting, identity-based leadership principles, and disciplined professional growth frameworks.

A structured collection of infrastructure troubleshooting reports, hardening procedures, monitoring deployments, recovery operations, and security investigations demonstrating applied systems administration and infrastructure security practices in real-world environments.
REPORT – Attack Surface Reduction and Service Hardening – v1.0.0
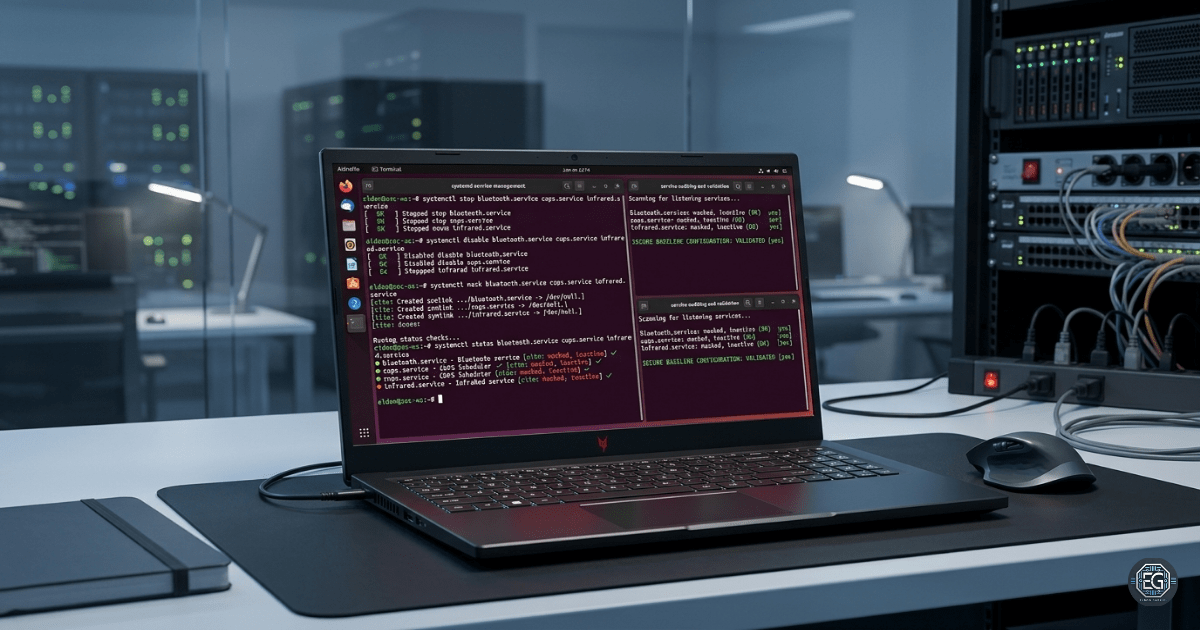
Technical implementation of attack surface. reduction by disabling and masking unnecessary system services on Ubuntu Server.
REPORT – Analyzing Legacy Network Services – v1.0.0
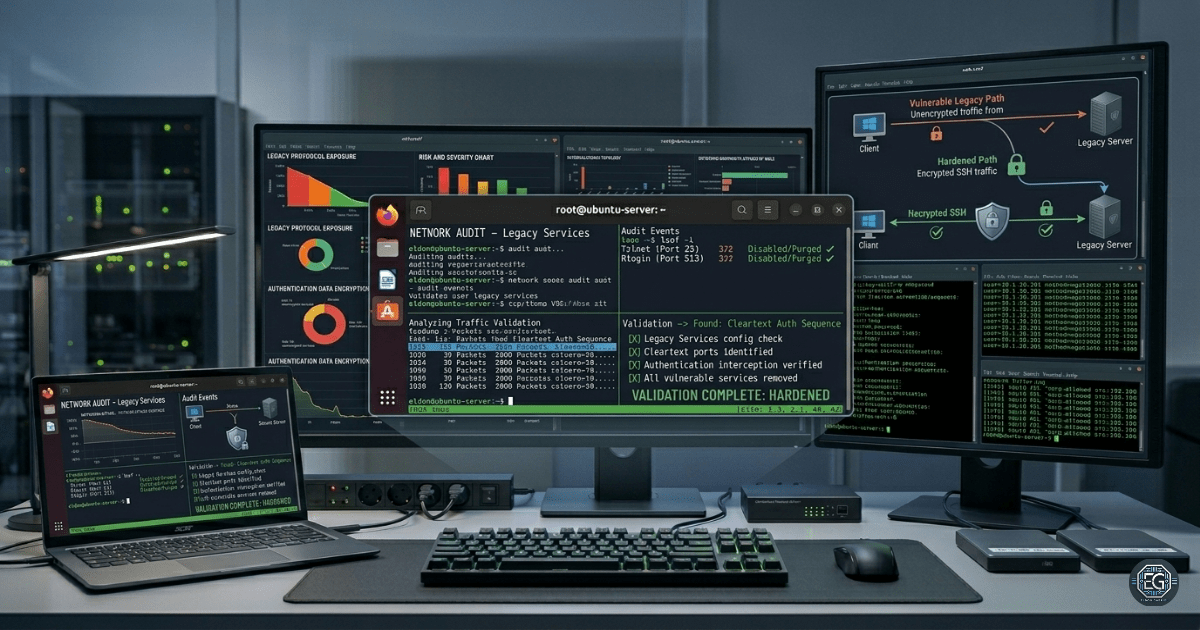
Technical implementation of a network service audit to demonstrate the risks of cleartext authentication protocols and network traffic interception.
REPORT – Network Service Auditing and Hardening – v1.0.0

Technical implementation of network service auditing and the disabling of insecure legacy protocols to reduce system attack surface.
REPORT – Securing Boot and Authentication Files – v1.0.0
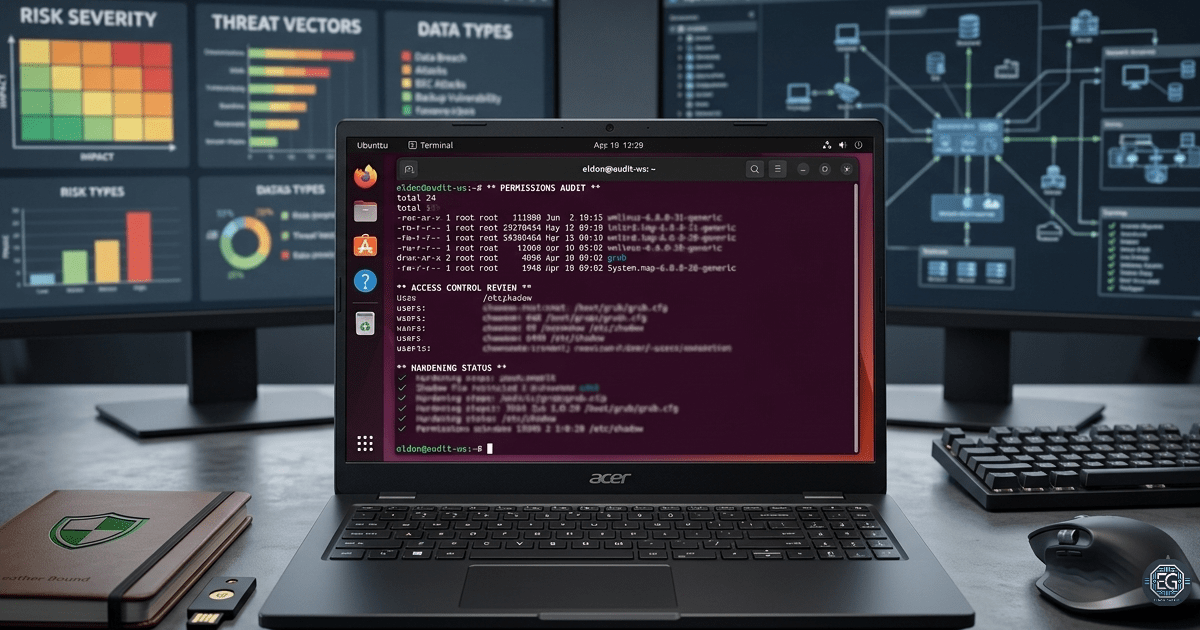
Technical implementation of permission hardening across critical system directories, bootloader configuration files, and authentication databases on Ubuntu Server.
REPORT – Password Strength Assessment – v1.0.0

Authorized password strength assessment on a Linux system using John the Ripper to identify weak passwords and improve account security.
REPORT – SSH Hardening with Multi-Factor Authentication – v1.0.0
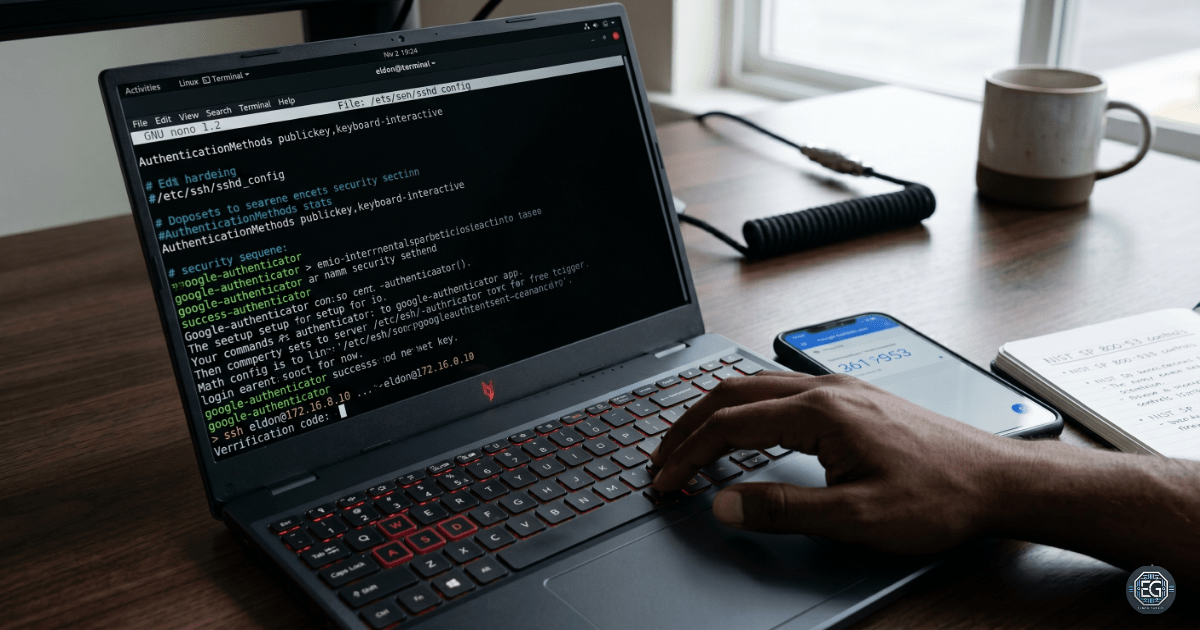
Technical implementation of SSH multi-factor authentication (MFA), public key authentication enforcement, and user access whitelisting using OpenSSH and PAM.
REPORT – Linux Hardening: PAM Authentication & Account Policy Enforcement – v1.0.0
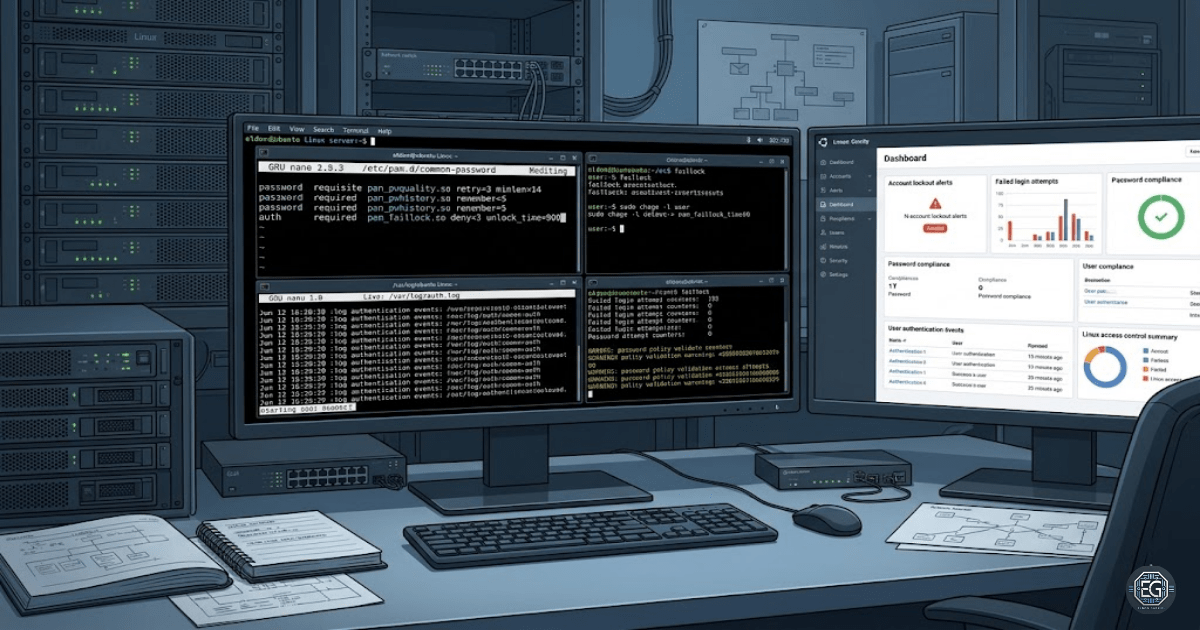
Technical implementation of password complexity enforcement, account lockout protection, and local authentication hardening using PAM.
REPORT – Linux Admin: Samba File Sharing Deployment and Validation – v1.0.0
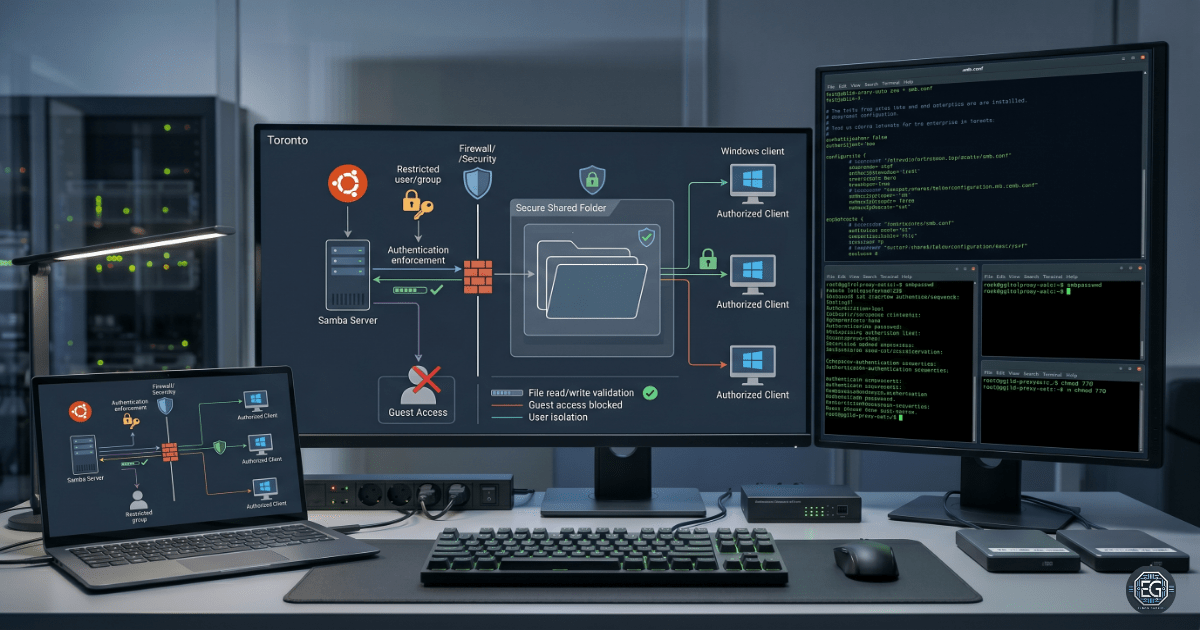
Technical deployment, access control validation, and cross-platform integration of a secure Samba file-sharing service.
REPORT – Linux Admin: Network File System (NFS) Deployment – v1.0.0
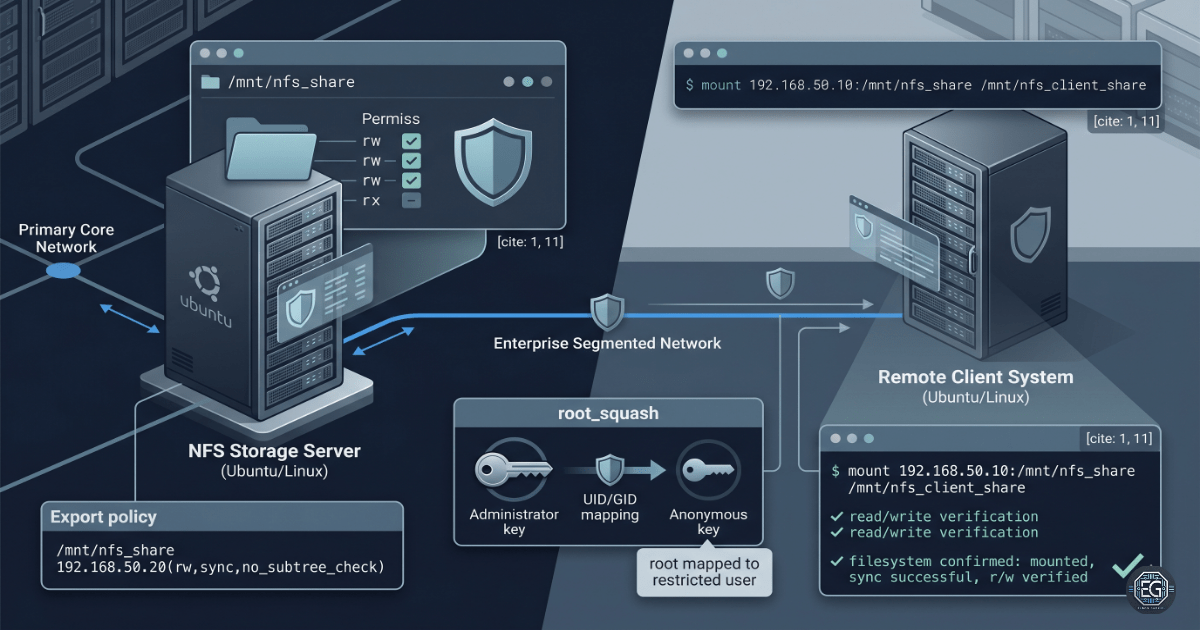
Technical deployment and security validation of a Network File System (NFS) environment.
REPORT – Linux Admin: Squid Proxy Configuration & Authentication – v1.0.0
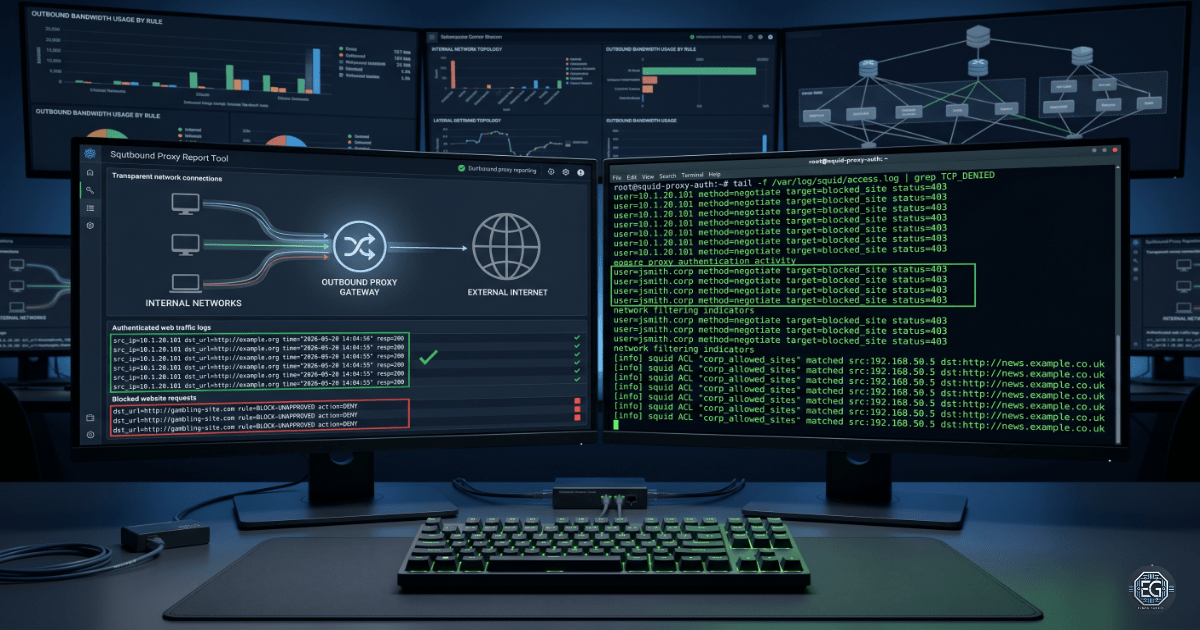
Technical implementation of a secure, authenticated Squid proxy server with domain-level web filtering.

