What I Studied
I analyzed a “lost” USB storage device found in a public area of a simulated healthcare facility (Rhetorical Hospital).
Tools and Techniques:
Simulated hardware write-blocking, VMware Workstation, Windows 10 Sandbox, and manual file header analysis.
Frameworks Applied:
NIST SP 800-83 (Guide to Malware Incident Prevention and Handling) and the social engineering (baiting) threat model.
What I Learned
Sandboxing is Mandatory:
I reinforced the discipline of never connecting untrusted media to a host OS. I configured a “host-only” virtual network to ensure any potential “phone-home” malware remained contained.
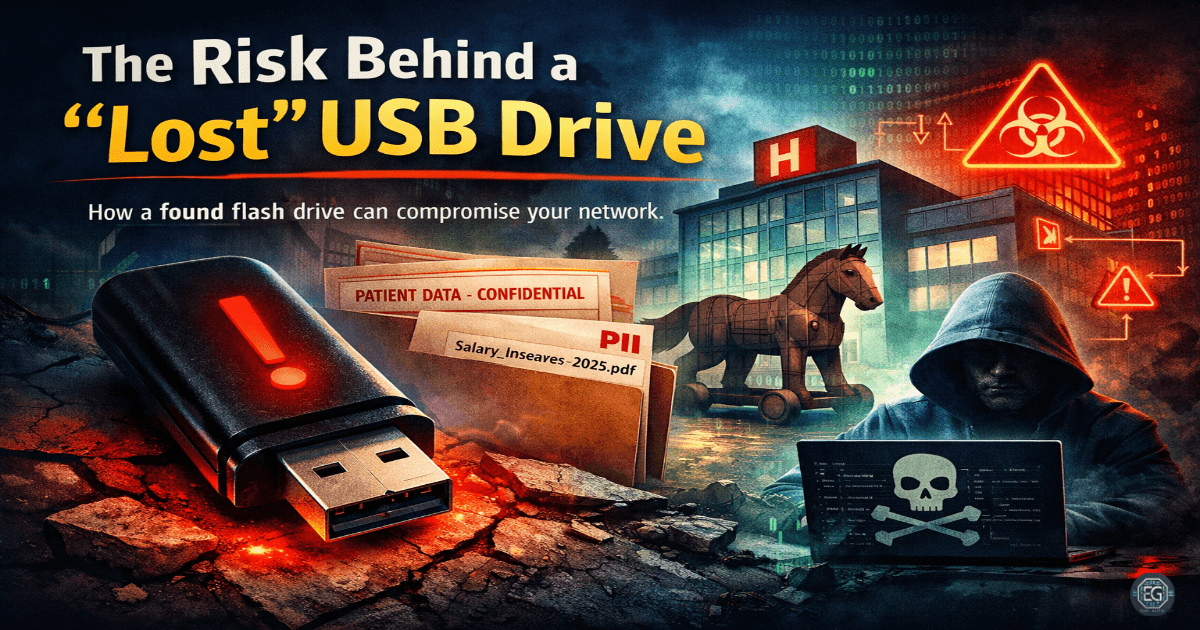
The “Bait” is Real:
Attackers use enticing file names (e.g., “Salary_Increases_2025.pdf”) to trigger human curiosity.
Compliance vs. Malware:
A USB threat is not always a virus. Unencrypted sensitive data on the device can create a major data breach under HIPAA or GDPR.
Why It Matters
In an enterprise environment, a single “lost” USB device can bypass millions of dollars in firewall protection if an employee plugs it into the internal network. This directly relates to system hardening (disabling AutoRun/AutoPlay) and operational defense.
Analogy:
If a firewall is the locked front door of a castle, a lost USB is a Trojan Horse carried inside by a well-meaning guard.
How It Maps to the Job / Framework
NICE Framework – Cyber Defense Incident Responder (CIR):
Reinforces the ability to investigate host-based artifacts and perform initial triage on suspicious media.
ASD Cyber Skills Framework – Systems Security (SSEC):
Demonstrates practical application of physical media security controls and workstation hardening.
Key Takeaways
- Isolation First: Never trust hardware; always analyze in a segmented or disposable environment.
- Policy > Technology: Technical controls are strongest when paired with user awareness training.
- Data Integrity: The presence of PII on portable media is a high-level risk that requires immediate reporting.
- Documentation: Risk must be translated into clear, professional reporting for stakeholders.
Proceed With Caution:
A USB device is not just storage. It is an untrusted endpoint. Treat it accordingly.
Related Projects
REPORT – USB Security Risk Assessment – v1.2.1