0.0 Executive Summary
This report documents the implementation of Local Group Policy Objects (GPOs) designed to restrict anonymous access and harden a Windows 10 system against adversary reconnaissance. The project successfully neutralized the threat of “Null Sessions” by preventing the anonymous enumeration of SAM accounts and shares.
By aligning the system with a hardened security baseline, the investigation verified that unauthorized enumeration attempts no longer return sensitive system details, effectively disrupting the initial reconnaissance phase of the cyber-attack lifecycle.
1.0 Anonymous Access & Recon Hardening
1.1 Project Description
The objective of this task was to secure a Windows 10 workstation by disabling legacy settings that allow unauthenticated users to gather information about the system. The project aimed to utilize the Local Group Policy Editor to bridge the gap between default permissive settings and a hardened security posture.
The environment focused on mitigating “Null Session” vulnerabilities, ensuring that internal identifiers such as user lists and network share names are shielded from unauthorized external or internal reconnaissance attempts.
1.2 Technical Task / Troubleshooting Process
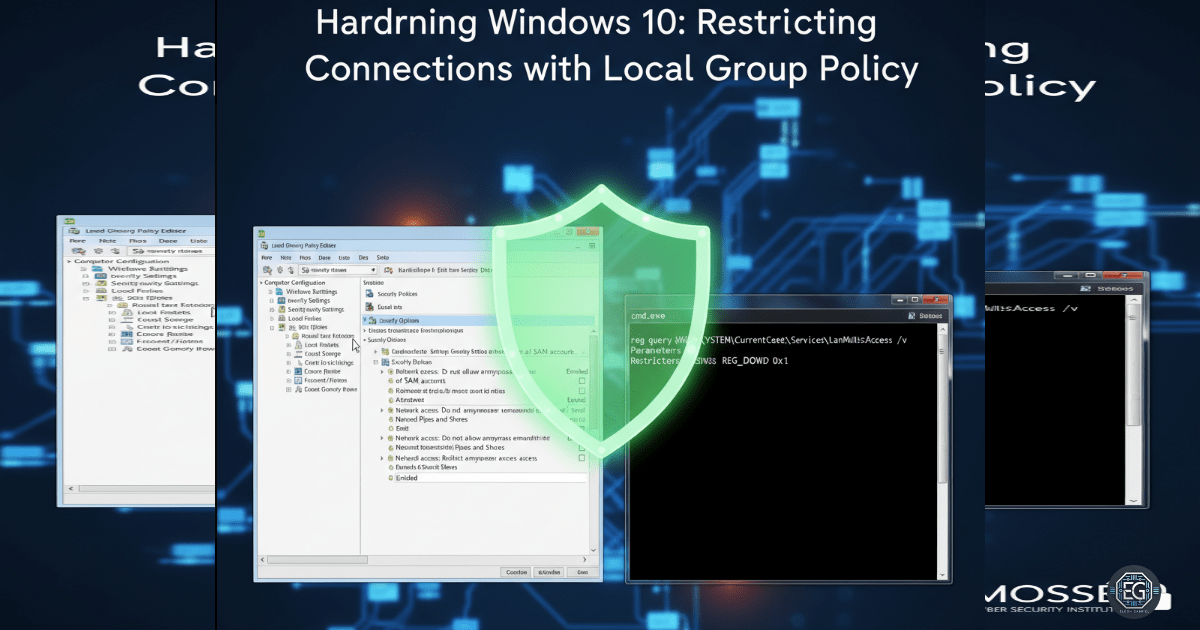
The process involved the systematic identification of policies that govern anonymous connections and the verification of their impact on the system registry.
Key Actions & Observations
-
Policy Identification: Located and configured GPOs specifically targeting “Network access: Do not allow anonymous enumeration of SAM accounts” and “shares.”
-
Registry Correlation: Established a direct link between the applied Group Policy settings and the underlying registry values to ensure configuration integrity.
-
Enumeration Testing: Attempted to perform user-and-share listing tests before and after policy application to measure defensive efficacy.
-
Hardening Demonstration: Observed that queries that previously returned account data were successfully blocked after the GPO refresh.
Root Cause: Default Windows configurations often allow anonymous “Null Sessions” to facilitate legacy compatibility, which inadvertently provides adversaries with a roadmap for targeted attacks.
1.3 Resolution and Validation
System hardening was finalized through registry queries and failed enumeration attempts to prove the new restrictions were active.
| Parameter | Configuration Value |
|---|---|
| Control Mechanism | Local Group Policy (GPO) |
| Primary Target | Anonymous SAM Enumeration |
| Primary Target | Anonymous Share Enumeration |
| Verification Tool | Registry Queries / Enumeration Tests |
Validation Steps
-
Registry Audit: Confirmed that the relevant system keys reflected the hardened state mandated by the Local GPO.
-
Negative Testing: Verified that unauthorized anonymous connections no longer produced results or system details.
-
Baseline Confirmation: Validated that the workstation was operating under a hardened baseline resistant to automated reconnaissance tools.
2.0: CONCLUSION
2.1 Key Takeaways
-
Reconnaissance Disruption: Blocking anonymous enumeration is a critical early-stage defense that prevents attackers from mapping the internal network.
-
Registry Synchronization: Understanding the link between Group Policy and the registry is vital for verifying that security controls are technically enforced.
-
Baseline Mitigation: Hardening system baselines directly mitigates common adversary techniques identified in frameworks like MITRE ATT&CK.
2.2 Security Implications & Recommendations
Risk: Adversary Reconnaissance via Null Sessions If anonymous connections are permitted, attackers can identify valid usernames and share paths to facilitate brute-force or lateral movement attacks.
Mitigation: Enforce “Do not allow anonymous enumeration” policies via GPO and monitor system security logs for failed anonymous login attempts.
Risk: Inconsistent Hardening Relying on manual local configurations across an enterprise leads to security gaps and administrative overhead.
Mitigation: Replicate the verified local configuration across the entire organization using domain-level GPOs and transition toward Kerberos authentication to further limit NTLM-based risks.