0.0 Executive Summary
This report documents the evaluation and hardening of a publicly accessible database server.
The objective was to reduce the risk of data theft and service disruption by addressing weak access controls and lack of authentication.
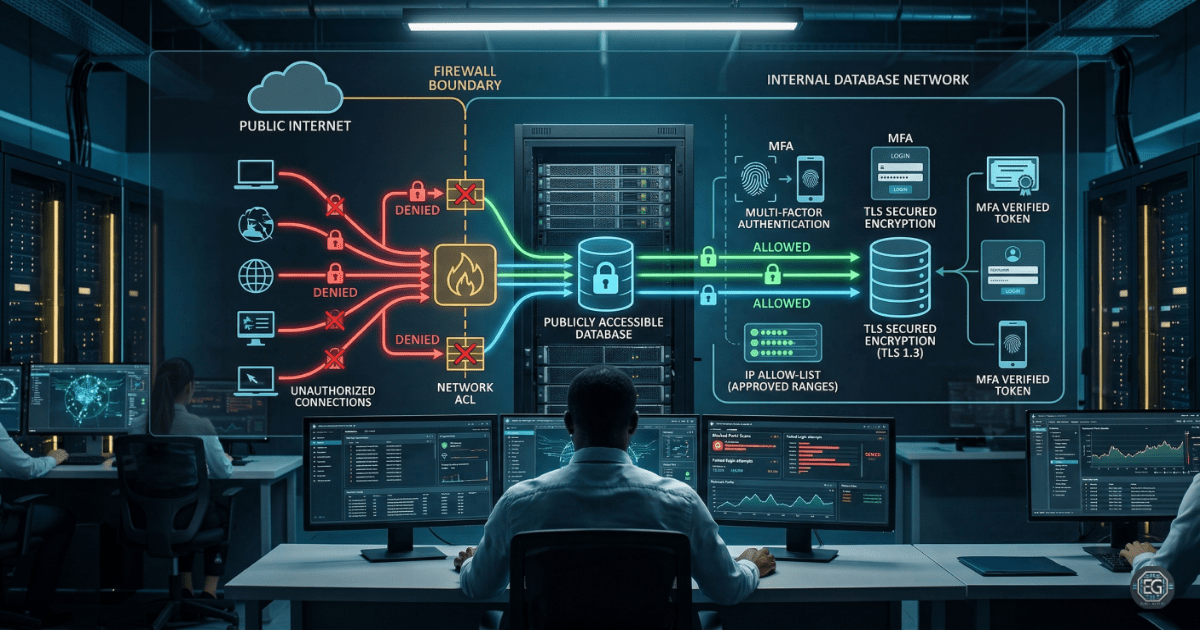
The result is an improved security posture achieved by replacing an open configuration with controlled measures, including firewalls, IP allow-listing, and Multi-Factor Authentication (MFA). These controls help protect sensitive systems and maintain secure global operations.
1.0 Server Security Evaluation
1.1 Project Description
The goal of this task was to establish a secure server baseline to prevent unauthorized access to sensitive data stored on remote infrastructure.
A risk-based approach was used to:
- Identify gaps in network segmentation and authentication
- Recommend Access Control Lists (ACLs) and Role-Based Access Control (RBAC)
- Improve visibility through logging and continuous monitoring
This helps reduce the risk of data tampering and unauthorized data access by closing exposed entry points.
1.2 Technical Task / Troubleshooting Process
The process focused on identifying weaknesses in the server environment and applying controls to mitigate those risks.
Key Actions & Observations
-
Reviewed system configuration and identified that the server was publicly accessible without authentication.
-
Applied IP allow-listing to restrict access to trusted corporate sources.
-
Enforced TLS encryption to secure data in transit and replace outdated SSL.
-
Strengthened access controls using firewalls and network-level ACLs.
-
Reduced the attack surface by patching known vulnerabilities and disabling unnecessary services.
-
Verified Multi-Factor Authentication (MFA) for administrative access.
-
Confirmed encryption was enabled for data at rest.
-
Documented configuration steps to support future audits and vulnerability assessments.
Root Cause: The server was deployed with open access to allow rapid global connectivity. This created a security gap by exposing the database to the public internet without proper controls. This was resolved by implementing a zero-trust approach with strict access enforcement.
1.3 Resolution and Validation
The server’s security posture was validated after applying the recommended controls.
| Parameter | Configuration Value |
|---|---|
| Management Tool | Firewall / ACL / IAM |
| Control State | Enforced |
| Security Mode | Hardened Baseline (Encryption/MFA) |
| Scope | Public-Facing Database Infrastructure |
Validation Steps
-
Attempted access from an unauthorized IP address and confirmed the firewall blocked the connection.
-
Verified that administrative logins required MFA before access was granted.
-
Confirmed that authorized internal services could connect to the database using secure TLS communication.
2.0: CONCLUSION
2.1 Key Takeaways
- Default open configurations can expose critical systems to external threats.
- IP allow-listing and RBAC are essential for controlling access in distributed environments.
- Validation testing confirms that security controls are properly enforced.
- Secure configurations must balance protection with usability for authorized users.
2.2 Security Implications & Recommendations
Risk: Data Theft and Tampering
Publicly exposed systems without authentication are frequent targets for attackers.
Mitigation: Restrict access using firewalls, IP allow-listing, and strong authentication mechanisms.
Risk: Use of Outdated Protocols
Legacy protocols such as SSL are vulnerable to interception and exploitation.
Mitigation: Enforce modern TLS protocols and ensure encryption for data in transit and at rest.
Best Practices
- Apply least privilege using RBAC and regular access reviews
- Automate patching and vulnerability scanning using centralized tools
- Validate system changes to ensure performance and availability are not impacted
- Maintain documentation for audits and compliance with frameworks such as NIST
Framework Alignment
- Aligns with NIST SP 800-53 (SC-7 Boundary Protection)
- Supports ISO 27001 (A.12.6.1) for vulnerability management
- Reinforces NIST CSF Protect and Detect functions through access control and monitoring