Introduction
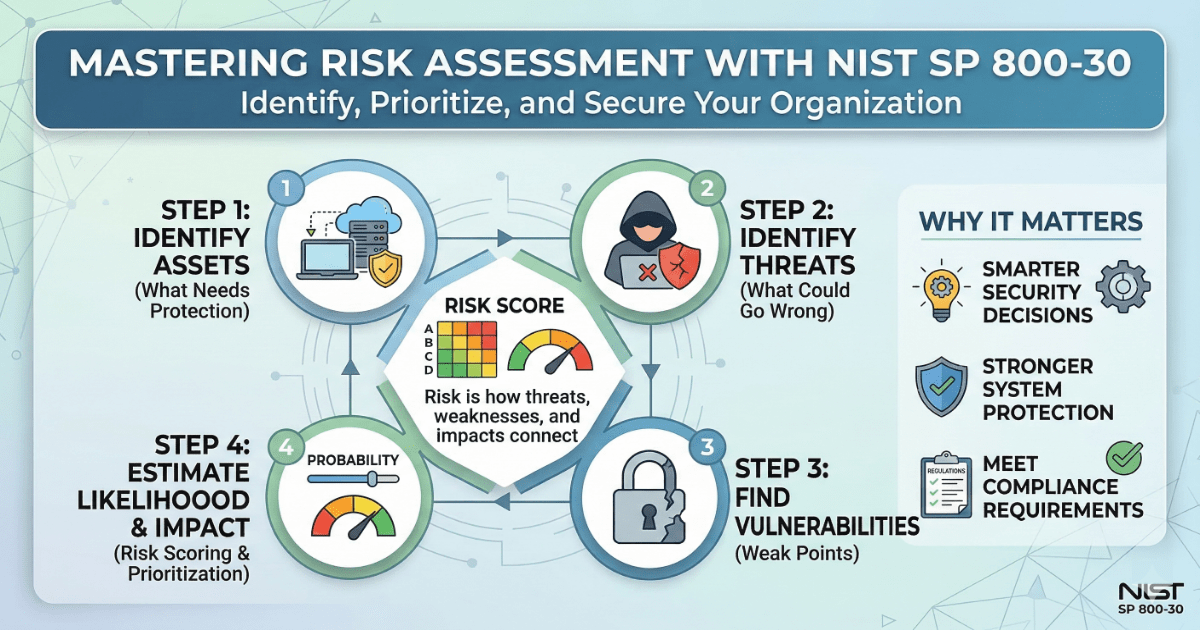
This exercise focused on performing a basic risk assessment using the NIST SP 800-30 framework. The goal was to understand how organizations identify risks and decide what needs to be fixed first.
What I Studied
- Asset identification: determining what needs protection
- Threat identification: understanding what could go wrong
- Vulnerability analysis: finding weak points in systems
- Risk evaluation: estimating likelihood and impact
A simple scoring method was used to rank risks. The process followed a structured approach so results could be repeated and compared.
What I Learned
- Risk is not just about threats. It depends on how threats, weaknesses, and impact connect.
- Small issues can become serious if they affect critical systems.
- Clear writing is important. If risk is not understood, it cannot be fixed.
- Too much detail can make reports harder to use.
I also learned that risk scoring can be overcomplicated. Keeping it simple made the results easier to explain.
Why It Matters
Risk assessment helps organizations decide what to fix first. Without it, teams may focus on low-impact issues while serious risks are ignored.
In real environments, this is like building maintenance. A broken light is less urgent than a broken lock on the front door.
This process supports:
- Better security decisions
- Stronger system protection
- Meeting compliance requirements
Related Projects
GUIDE – Risk Assessment Adapted from NIST SP 800-30 Rev. 1 – v1.0.2
Reflection & Next Steps
This exercise strengthened my understanding of structured risk analysis and decision-making. I will continue building on this by applying risk frameworks to more complex systems and scenarios.