0.0 Executive Summary
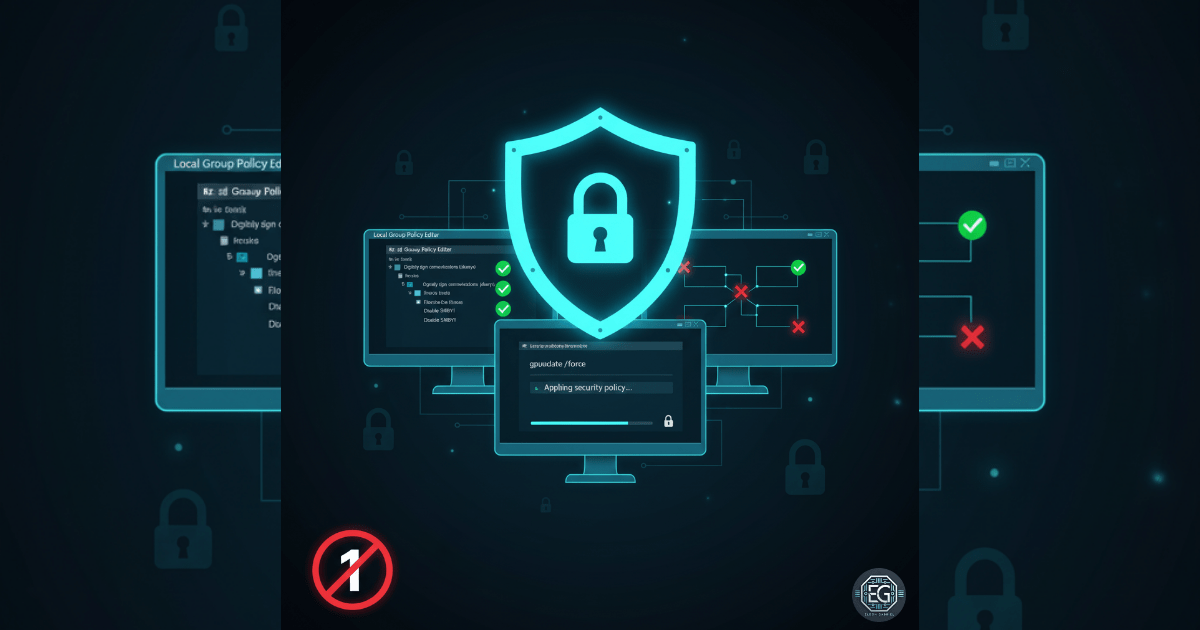
This report documents the implementation of security hardening measures for Server Message Block (SMB) communications on a Windows 10 endpoint. The project successfully mitigated risks associated with credential theft and session hijacking by enforcing SMB signing, disabling the deprecated SMBv1 protocol, and configuring idle session timeouts. These actions align with modern security standards to prevent common exploitation techniques such as SMB relay attacks and unauthorized lateral movement.
1.0 SMB Hardening for Credential Theft Protection
1.1 Project Description
The objective of this task was to secure SMB communications to protect against intercepted credentials and unauthorized access. The project aimed to utilize Local Group Policy and registry modifications to establish a hardened communication baseline. The environment focused on transitioning the system away from legacy protocols and ensuring that all network file sharing activities are authenticated and encrypted, thereby reducing the success rate of man-in-the-middle (MITM) attacks.
1.2 Technical Task / Troubleshooting Process
The process involved a combination of policy enforcement and manual registry adjustments to strip insecure legacy features.
Key Actions & Observations
-
Policy Enforcement: Configured Local Group Policy to mandate SMB signing for both client and server communications.
-
Protocol Deprecation: Modified the Windows Registry to explicitly disable SMBv1, eliminating a high-risk legacy attack vector.
-
Session Management: Set mandatory idle session timeouts to ensure that inactive connections are automatically terminated, reducing the window for session hijacking.
-
Security Audit: Verified that “Send unencrypted passwords to third-party SMB servers” was disabled to prevent cleartext credential exposure.
Root Cause: Reliance on default, unhardened SMB settings and the presence of legacy SMBv1 protocols were identified as primary vulnerabilities for credential relay and theft.
1.3 Resolution and Validation
Operational hardening was finalized by verifying the application of security policies and the removal of insecure protocols.
| Parameter | Configuration Value |
|---|---|
| SMB Signing | Required / Enabled |
| SMBv1 Status | Disabled (Registry) |
| Idle Timeout | Configured |
| Tooling Used | gpedit.msc / regedit |
Validation Steps
- Registry Verification: Confirmed the
SMB1key was set to0to ensure the protocol cannot be initialized. - Policy Check: Verified via the Local Group Policy Editor that all SMB signing and session limit settings were successfully applied.
- Connectivity Audit: Confirmed that the system maintained secure connectivity with trusted devices while rejecting unsigned or insecure requests.
2.0: CONCLUSION
2.1 Key Takeaways
-
Protocol Hygiene: Disabling outdated services like SMBv1 is a fundamental requirement for modern infrastructure security.
-
Data Integrity: SMB signing ensures that network data is authentic and has not been tampered with during transit.
-
Session Control: Automated timeouts are an effective low-overhead control for reducing the risk of unauthorized lateral movement.
2.2 Security Implications & Recommendations
Risk: SMB Relay Attacks Unsigned SMB traffic allows attackers to intercept and relay authentication hashes to gain unauthorized access to other systems.
Mitigation: Enforce SMB signing across all network endpoints and mandate SMB 3.1.1 encryption where supported by the infrastructure.
Risk: Credential Theft via Legacy Protocols Outdated protocols like SMBv1 lack modern security features and are highly susceptible to known exploits and credential harvesting.
Mitigation: Conduct a network-wide audit to identify and disable all instances of SMBv1, Telnet, and other insecure legacy communication methods.