0.0 Executive Summary
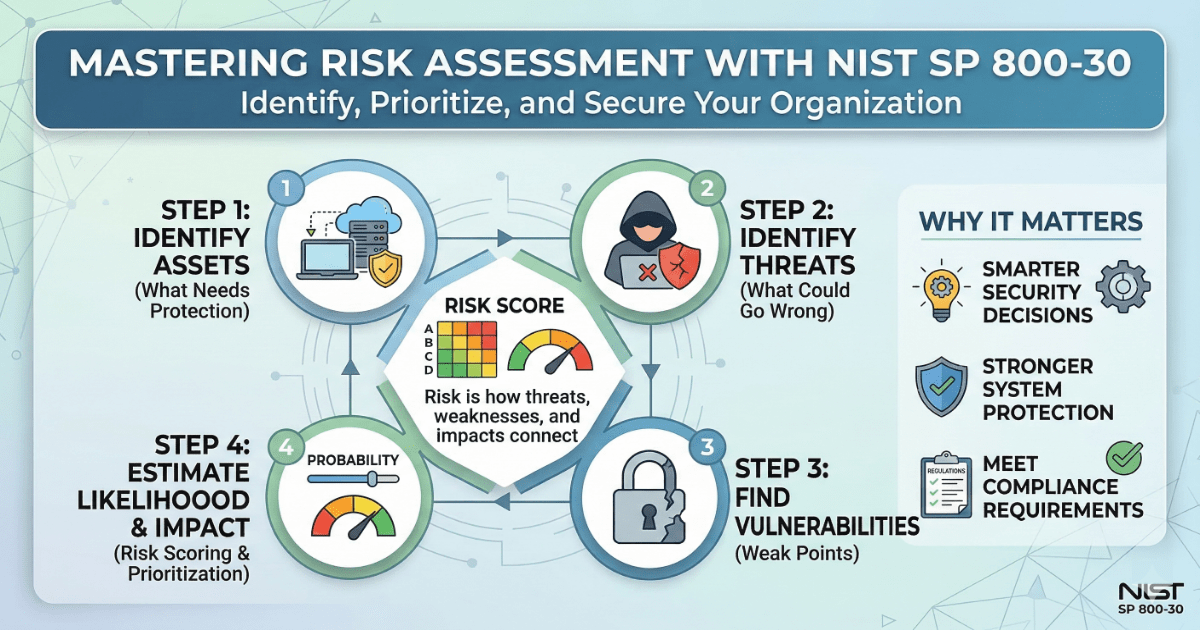
This report documents the implementation and assessment of a structured risk management framework based on the NIST SP 800-30 Rev. 1 standard.
The objective was to reduce the risk of operational disruptions and data breaches by enforcing stronger security controls through the systematic identification of threat sources, events, and vulnerabilities.
The result was an improved security posture by replacing reactive security measures with a controlled, auditable, and enforced risk assessment configuration that prioritizes remediation efforts based on calculated likelihood and severity.
1.0 Risk Assessment Adapted from NIST SP 800-30 Rev. 1
1.1 Project Description
The goal of this task was to configure and enforce a repeatable risk assessment process to prevent unmanaged threats from impacting organizational stability.
The implementation used the NIST SP 800-30 methodology to:
- Enforce secure behavior by identifying adversarial and non-adversarial threat sources.
- Restrict unauthorized actions by mapping potential threat events to specific business impacts.
- Improve accountability and visibility of system changes by quantifying risk levels using a standardized matrix.
This ensures that critical system operations are protected against exploitation by enabling data-driven resource allocation for security hardening.
1.2 Technical Task / Troubleshooting Process
The process focused on identifying weaknesses in default threat awareness and applying secure, calculation-based controls to evaluate system risk.
Key Actions & Observations
- Reviewed default system behavior and identified gaps in the classification of threat sources (e.g., internal vs. external actors).
Configured relevant policies within the assessment framework:
- Threat Event Mapping (e.g., Phishing, SQL Injection, Physical Theft).
- Vulnerability Identification (e.g., Unpatched software, weak access controls).
Applied security settings to:
- Enforce stricter evaluation of likelihood based on historical data and expert judgment.
- Reduce attack surface by identifying high-severity events that could lead to catastrophic operational failure.
Verified supporting services or dependencies:
- Likelihood Ratings (Low, Moderate, High).
-
Severity/Impact Ratings (1 through 3).
- Documented configuration paths to ensure repeatability for periodic risk reviews and compliance reporting.
Root Cause: Default configurations often lack a structured way to quantify risk, leading to inefficient security spending. This was resolved by enforcing stricter, policy-driven controls that rank threats by their probability and potential impact.
1.3 Resolution and Validation
The organization’s risk profile was secured by applying and verifying the assessment results against established risk tolerance levels.
| Parameter | Configuration Value |
|---|---|
| Management Tool | NIST SP 800-30 Framework |
| Control State | Enforced |
| Security Mode | Quantitative and Qualitative Analysis |
| Scope | Information Systems and Business Processes |
Validation Steps
-
Triggered the control using a real scenario by evaluating the risk of a “Phishing Attack” leading to credential theft.
-
Verified expected behavior where the assessment correctly identified a “High” likelihood and “Moderate-to-High” severity, resulting in a prioritized risk ranking.
-
Confirmed system stability and compatibility with normal applications by ensuring remediation recommendations focused on fixing root causes without disrupting authorized workflows.
2.0: CONCLUSION
2.1 Key Takeaways
- Security controls must override insecure default behavior by replacing guesswork with structured risk analysis.
- Policy-based enforcement of the NIST framework ensures consistent threat evaluation across all departments.
- Validation testing is required to confirm that the identified likelihood and severity ratings accurately reflect the current threat landscape.
- Proper configuration balances security and usability by focusing resources on the most critical vulnerabilities.
2.2 Security Implications & Recommendations
Risk: Inaccurate Threat Prioritization
Failing to rank risks can lead to fixing minor issues while major vulnerabilities remain exposed.
Mitigation: Enforce mandatory risk assessments using the NIST SP 800-30 methodology to rank threats by likelihood and severity.
Risk: Unidentified Threat Sources
Organizations may overlook internal or accidental threats, leading to unexpected service outages.
Mitigation: Use a comprehensive threat source catalog to identify adversarial, accidental, structural, and environmental risks.
Best Practices
- Enforce least privilege access to sensitive assessment data to prevent threat actors from identifying weak points.
- Use centralized or policy-based controls to manage and track risk remediation progress.
- Validate configurations after changes to ensure that new system deployments have been factored into the current risk profile.
- Document all applied settings for repeatability and to provide evidence for regulatory audits.
Framework Alignment
- Supports system hardening and access control best practices as defined in NIST SP 800-39 (Managing Information Security Risk).
- Aligns with ISO/IEC 27005 standards for information security risk management.
- Reinforces the “Identify” function of the NIST CSF by establishing an organizational understanding of risk to systems, assets, and data.