0.0 Executive Summary
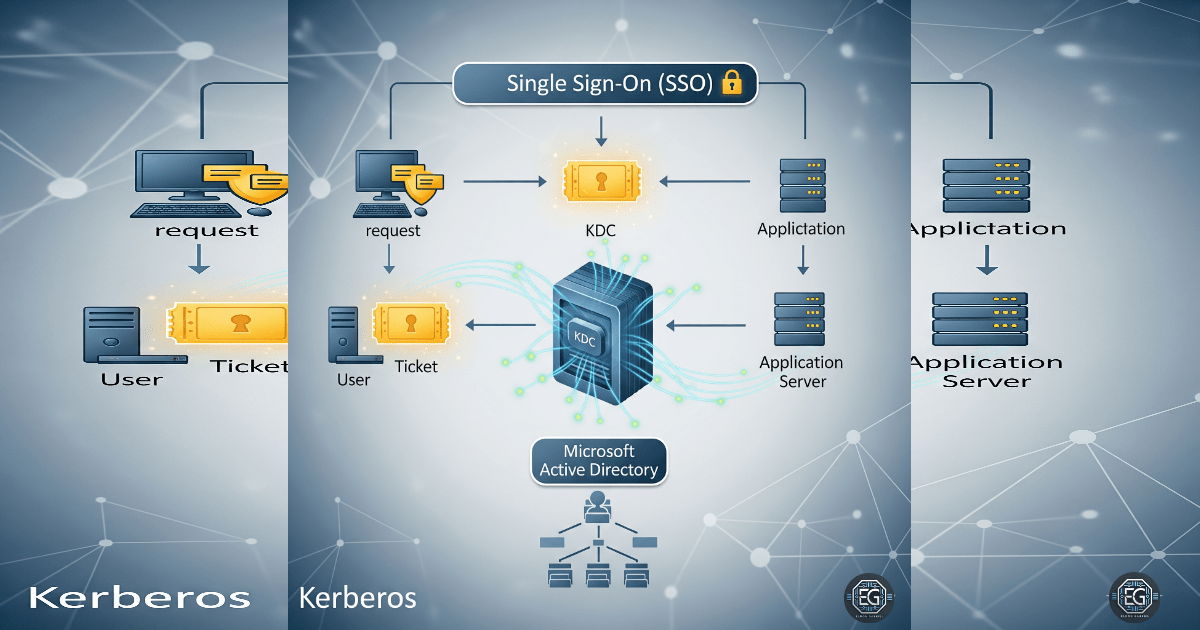
This report explains how authentication was secured in a Windows enterprise environment using the Kerberos protocol.
The goal was to reduce risks such as credential theft and unauthorized lateral movement. This was done by using a ticket-based authentication system instead of sending passwords across the network.
The final result improved security by replacing older methods like NTLM with encrypted Kerberos tickets. This protects user credentials and controls access to network resources.
1.0 Kerberos Authentication Protocol
1.1 Project Description
The goal of this task was to set up a secure and scalable authentication system for network access.
Kerberos was used to:
- Authenticate users through a trusted central service (Key Distribution Center - KDC)
- Issue secure, time-limited tickets for access
- Control access to services without sending passwords over the network
These controls help protect systems such as file servers and databases by using Single Sign-On (SSO) and mutual authentication.
1.2 Technical Task / Troubleshooting Process
The process focused on replacing weak authentication methods and applying secure Kerberos settings.
Key Actions & Observations
- Reviewed system settings and identified the use of legacy NTLM authentication
Configured core Kerberos components:
- Key Distribution Center (KDC)
- Ticket-Granting Service (TGS)
Applied security controls by:
- Enforcing encrypted ticket exchanges
- Setting short lifetimes for authentication tickets
Reduced risk of attacks such as:
- Kerberoasting
- Golden Ticket and Silver Ticket attacks
Verified supporting services:
- Authentication Service (AS)
-
Service Ticket validation
- Documented all configurations for use in Active Directory environments
Root Cause:
Older authentication methods like NTLM are still enabled for compatibility but expose systems to attacks. This was fixed by enforcing Kerberos as the primary authentication method and using secure ticket-based controls.
1.3 Resolution and Validation
The authentication system was secured and tested to confirm correct Kerberos operation.
| Parameter | Configuration Value |
|---|---|
| Management Tool | Active Directory / KDC |
| Control State | Enforced |
| Security Mode | Mutual Authentication / SSO |
| Scope | Domain Environment |
Validation Steps
-
Requested access to a network service such as a file share
-
Verified that the system issued a Ticket-Granting Ticket (TGT)
-
Confirmed a Service Ticket (ST) was issued for the requested resource
-
Verified access without needing to re-enter credentials
-
Confirmed system stability and normal operation
2.0 CONCLUSION
2.1 Key Takeaways
- Kerberos provides secure, ticket-based authentication
- Legacy methods like NTLM increase security risk
- Centralized authentication improves control and visibility
- Ticket lifetimes help limit the impact of attacks
- Proper setup balances strong security with user convenience
2.2 Security Implications and Recommendations
Risk: Kerberoasting Attacks
Attackers may try to capture and crack service account tickets.
Mitigation:
Use strong passwords for service accounts and monitor for unusual ticket activity.
Risk: Ticket Forgery (Golden/Silver Tickets)
Attackers may create fake tickets if key systems are compromised.
Mitigation:
Protect the Key Distribution Center (KDC) and regularly rotate the KRBTGT account password.
Best Practices
- Apply least privilege so users only access required services
- Use Active Directory to manage and audit authentication
- Enforce strong encryption such as AES-256
- Regularly review logs for unusual authentication behavior
- Document all configurations for auditing and troubleshooting
Framework Alignment
- Supports Zero Trust principles (NIST SP 800-207)
- Aligns with ISO 27001 requirements for secure logon
- Supports the NIST Cybersecurity Framework by strengthening identity and access control