0.0 Executive Summary
This report documents the implementation of security controls following a significant data breach at a social media organization.
The objective was to reduce the risk of unauthorized access and data loss by strengthening identity management, credential handling, and network defenses.
The result is an improved security posture achieved by replacing insecure defaults such as single-factor authentication and overly permissive firewall rules with controlled, auditable configurations aligned with industry hardening practices.
1.0 Post-Breach Security Recommendations
1.1 Project Description
The goal of this task was to establish a post-breach recovery framework to prevent future compromises of customer data.
A vulnerability assessment approach was used to:
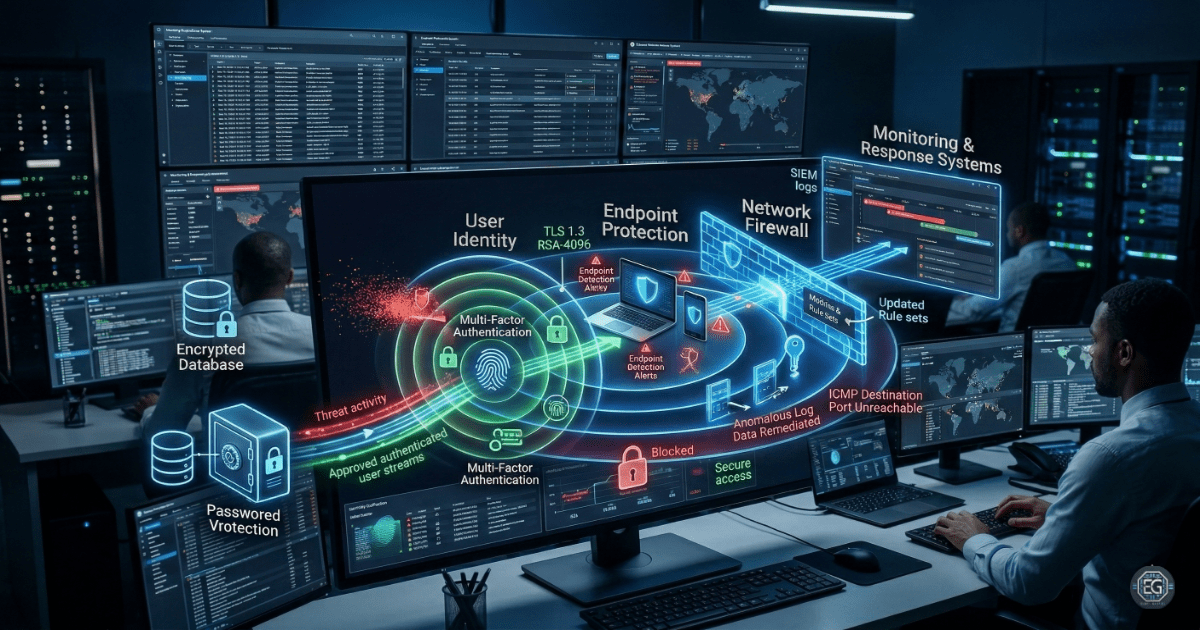
- Enforce Multi-Factor Authentication (MFA) across all accounts
- Improve credential security through centralized password management
- Increase visibility through firewall audits and log monitoring
This helps protect against common attack methods such as phishing and credential stuffing, which were contributing factors in the breach.
1.2 Technical Task / Troubleshooting Process
The process focused on identifying weaknesses that allowed the breach and applying controls to address them.
Key Actions & Observations
- Reviewed system behavior and identified the absence of MFA as a key weakness that allowed attackers to use stolen credentials.
Implemented remediation policies including:
- Enterprise password management to replace insecure storage methods
-
Mandatory MFA enrollment for all users and administrators
- Strengthened access controls by updating firewall rules and removing overly permissive or outdated entries
- Deployed endpoint detection and response (EDR) tools to monitor for suspicious activity and lateral movement
Verified supporting systems including:
- System log integrity
-
User behavior monitoring through SIEM integration
- Documented all configuration steps to support repeatability and future audits
Root Cause: The environment relied on single-factor authentication and static firewall rules. These controls were insufficient against credential-based attacks. This was resolved by implementing layered security controls and enforcing stricter policies across identity and network systems.
1.3 Resolution and Validation
The organization’s security posture was improved by applying and verifying the recommended controls.
| Parameter | Configuration Value |
|---|---|
| Management Tool | MFA / Firewall / Password Manager |
| Control State | Enforced |
| Security Mode | Defense-in-Depth |
| Scope | Enterprise Infrastructure and User Accounts |
Validation Steps
-
Attempted login using only a password and confirmed access was denied until a second factor was provided.
-
Verified that updated firewall rules blocked unauthorized attempts to access restricted internal systems.
-
Confirmed that normal business operations continued without disruption under the new security controls.
2.0: CONCLUSION
2.1 Key Takeaways
- Security controls must replace insecure default settings to reduce the impact of credential theft.
- Enforcing MFA significantly reduces the risk of unauthorized access.
- Validation testing ensures that insecure configurations have been fully removed.
- Security and usability must be balanced by providing tools such as password managers to support secure user behavior.
2.2 Security Implications & Recommendations
Risk: Credential Theft
Without MFA, a single compromised password can grant access to systems.
Mitigation: Enforce MFA across all systems and applications.
Risk: Firewall Misconfiguration
Old or overly permissive rules can allow unauthorized access or lateral movement.
Mitigation: Conduct regular firewall audits and apply least privilege principles.
Best Practices
- Apply least privilege access to limit the impact of compromised accounts
- Monitor logs and alerts using centralized SIEM tools
- Review and validate configurations after each change
- Maintain documentation to support audits, troubleshooting, and incident response
Framework Alignment
- Aligns with NIST SP 800-53 for identity and authentication controls
- Supports ISO 27001 (A.9.4.2) for secure log-on procedures
- Aligns with NIST CSF Protect and Recover functions by strengthening access controls and addressing post-incident vulnerabilities