0.0 Executive Summary
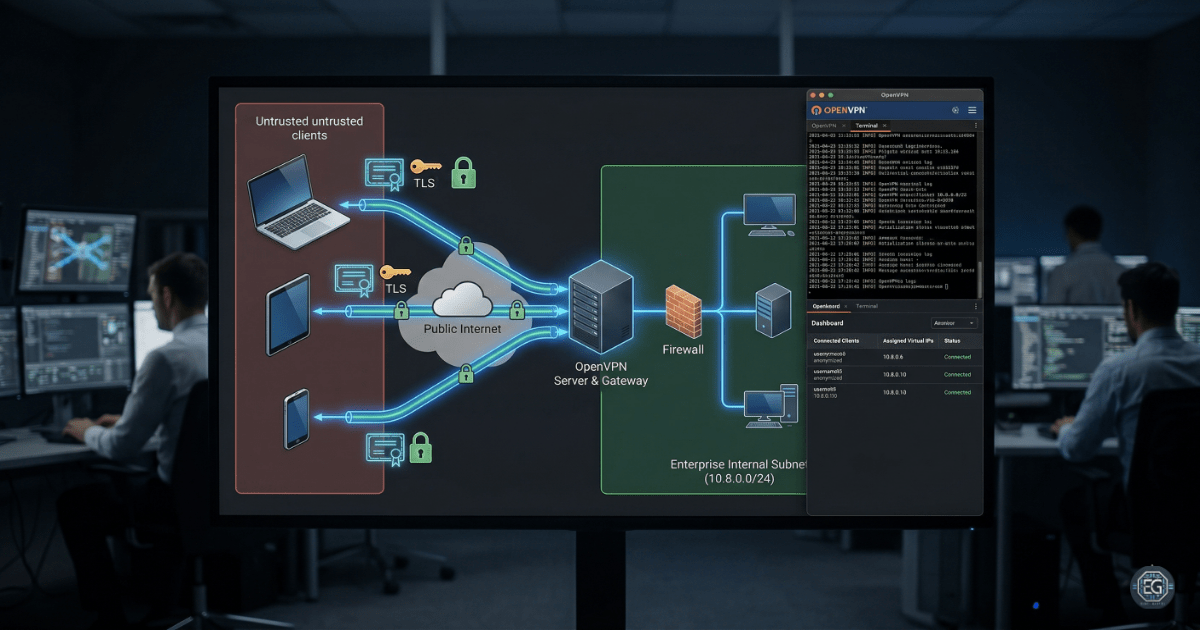
This report documents the deployment and hardening of an OpenVPN remote access solution on a Linux-based system.
The objective was to reduce the risk of data interception and unauthorized access by implementing stronger security controls. These controls include certificate-based authentication and encrypted tunnels for remote clients.
The result is a more secure remote access environment that replaces direct connections with a controlled and auditable VPN configuration. This was validated by successfully establishing tunnels, assigning internal IP addresses, and confirming internet traffic routing through the VPN gateway.
1.0 OpenVPN Remote Access VPN Deployment
1.1 Project Description
The goal of this task was to configure a secure remote access VPN to protect client traffic over public or untrusted networks.
OpenVPN was used to:
- Enforce secure access through a Public Key Infrastructure (PKI) with certificate-based authentication
- Protect traffic by routing all client communication through an encrypted tunnel (full tunneling)
- Improve visibility by validating routing tables and reviewing connection logs
This setup helps protect remote administrative tasks and internal system access from eavesdropping and man-in-the-middle attacks.
1.2 Technical Task / Troubleshooting Process
The process focused on identifying weaknesses in default remote access methods and applying certificate-based security controls.
Key Actions & Observations
-
Reviewed default system behavior and identified the need for a secure tunneling protocol that supports NAT and firewall traversal.
-
Configured OpenVPN server settings using Easy-RSA for PKI management.
-
Created client configuration files (.ovpn) with embedded certificates and keys.
-
Enforced authentication using unique client certificates instead of static passwords.
-
Enabled IP forwarding and configured NAT to allow traffic to route through the VPN server.
-
Verified TUN/TAP interface initialization on the server.
-
Confirmed allocation of the virtual subnet (10.8.0.0/24) to connected clients.
-
Documented all configuration steps to support future scaling and repeatability.
Root Cause: Standard internet connections do not provide encryption or identity verification for remote access. This was addressed by implementing OpenVPN with TLS-based encryption and certificate authentication.
1.3 Resolution and Validation
The remote access environment was secured by verifying tunnel connectivity and routing behavior.
| Parameter | Configuration Value |
|---|---|
| Management Tool | OpenVPN / Easy-RSA |
| Control State | Active |
| Security Mode | Certificate-Based Authentication |
| Scope | Remote Client-to-Server Tunneling |
Validation Steps
-
Initiated a VPN connection from a Linux client and confirmed assignment of a virtual IP address (10.8.0.x).
-
Ran routing verification (
tracert 8.8.8.8) and confirmed the first hop was the VPN gateway (10.8.0.1), indicating full tunneling was active. -
Performed connectivity tests using ICMP to confirm stable communication.
-
Verified that traffic was encrypted and passed through the VPN tunnel without disruption to normal applications.
2.0: CONCLUSION
2.1 Key Takeaways
- Remote connections must be secured using encryption to prevent exposure of sensitive data.
- Certificate-based authentication ensures that only trusted clients can access internal resources.
- Validation testing is required to confirm that full tunneling is functioning correctly and that no traffic bypasses the VPN.
- A properly configured VPN provides both security and usability for remote access to internal systems.
2.2 Security Implications & Recommendations
Risk: Certificate and Private Key Compromise
If a private key is exposed, an attacker could impersonate a valid user.
Mitigation: Apply strict file permissions to certificate files and implement Multi-Factor Authentication (MFA) as an additional control.
Risk: Over-Permissive Network Access
VPN users may gain access to more of the internal network than necessary.
Mitigation: Apply least privilege principles using firewall rules to restrict access to required subnets and services only.
Best Practices
- Regularly audit and revoke certificates for inactive or unauthorized users.
- Log authentication events and tunnel activity for monitoring and incident response.
- Verify routing and NAT configurations after any changes to ensure proper traffic flow.
- Maintain documentation of configurations to support troubleshooting and system maintenance.
Framework Alignment
- Aligns with NIST SP 800-113 guidance for secure VPN implementations
- Supports ISO 27001 (A.13.1.2) for network service security
- Aligns with the NIST CSF Protect function by securing communication channels and enforcing identity verification