0.0 Executive Summary
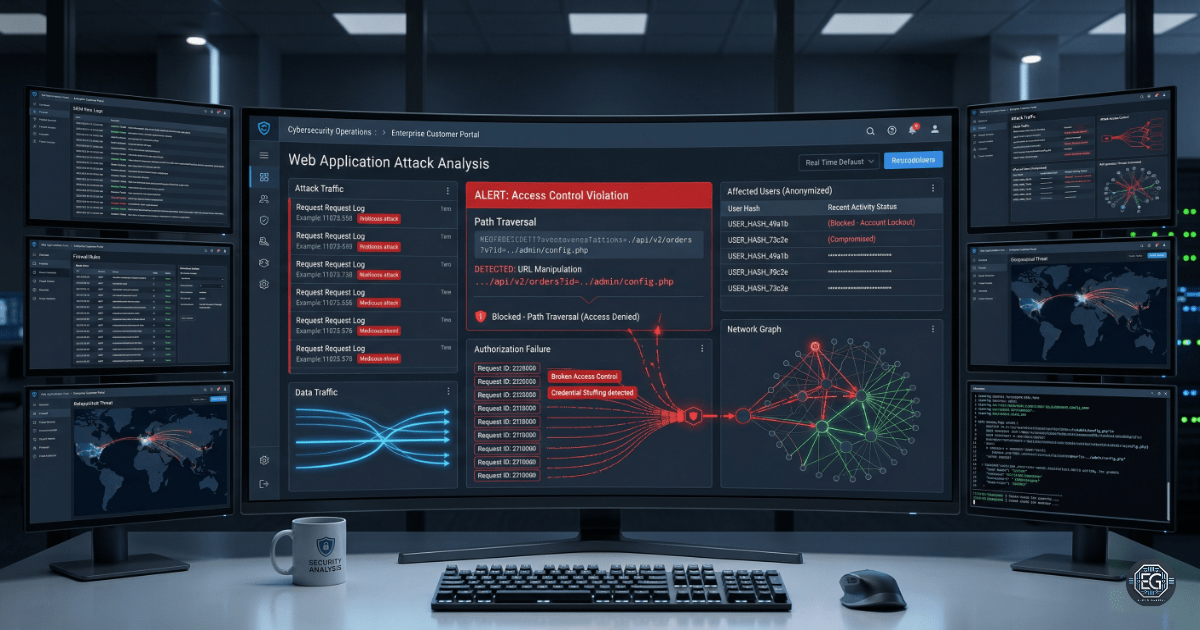
This report explains a security incident that occurred on December 28, 2024, affecting an e-commerce web application. An attacker gained unauthorized access to customer data by exploiting a weakness in the application. Around 50,000 records were exposed, including personal and financial information. The estimated financial impact was $100,000.
The root cause was a forced browsing vulnerability. This allowed the attacker to access customer records by changing order numbers in the URL.
The issue has been resolved. Security controls were improved by enforcing authentication, restricting URL access, and validating user permissions. Affected customers were notified and provided with identity protection services.
1.0 Incident Report: E-Commerce Data Breach
1.1 Project Description
This investigation was conducted after a ransom demand was received from a threat actor claiming to have stolen customer data.
The goal was to identify how the breach occurred, confirm the scope of the impact, and implement controls to prevent it from happening again.
The investigation focused on:
- Reviewing application behavior and access controls
- Analyzing web server logs
- Testing for unauthorized access to customer data
The findings confirmed that the purchase confirmation system allowed unauthorized access due to weak access control.
1.2 Technical Analysis
The investigation focused on identifying the vulnerability and confirming how the attacker accessed the data.
Key Findings
- Purchase confirmation pages used predictable order numbers in the URL
- The application did not verify if the user was authorized to view the data
- Logs showed a high number of requests for sequential order numbers
- These requests matched the timeframe of the data breach
Root Cause
The application did not enforce proper access control.
An attacker could change the order number in the URL and view other customers’ records without logging in as that user.
1.3 Resolution and Validation
The vulnerability was fixed and security controls were updated.
| Parameter | Status |
|---|---|
| Incident Status | Closed |
| Impacted Records | 50,000 |
| Vulnerability Type | Forced Browsing (Broken Access Control) |
| Remediation | Completed |
Validation Steps
- Tested access to purchase pages without login. Access is now blocked.
- Verified that users can only view their own orders.
- Confirmed URL restrictions are enforced.
- Ran vulnerability scans and tests to confirm the issue is resolved.
2.0 Conclusion
2.1 Key Takeaways
- Weak access control led to the data breach
- Predictable URLs made it easy to access customer data
- Log analysis helped identify the attack pattern
- Proper validation and testing are critical before deployment
2.2 Security Implications and Recommendations
Key Risks
Unauthorized Data Access
Sensitive data was exposed due to weak access control.
Predictable URL Structure
Sequential order numbers allowed easy data enumeration.
Recommended Actions
Technical Controls
- Enforce strict access control on all sensitive pages
- Require authentication for all customer data access
- Replace sequential IDs with random identifiers
- Monitor logs for unusual access patterns
- Perform regular security testing
Operational Controls
- Train developers on secure coding practices
- Perform regular code reviews
- Maintain a formal incident response process
Framework Alignment
- OWASP Top 10: Broken Access Control
- NIST SP 800-53: Access Control (AC-3)
- NIST CSF: Detect and Respond functions
This report demonstrates how a simple application weakness can lead to large-scale data exposure. Strengthening access control and validation is critical to preventing similar incidents.