- Security Operations 12
- Identity Security 9
- Infrastructure and Systems 7
- Networking 4
- OSINT Investigation 3
- Governance and Risk 1
- Operational Approach 1
- Operational Resilience 1
Security Operations
SOP – Secure Linux Management with Cockpit – v1.0.1
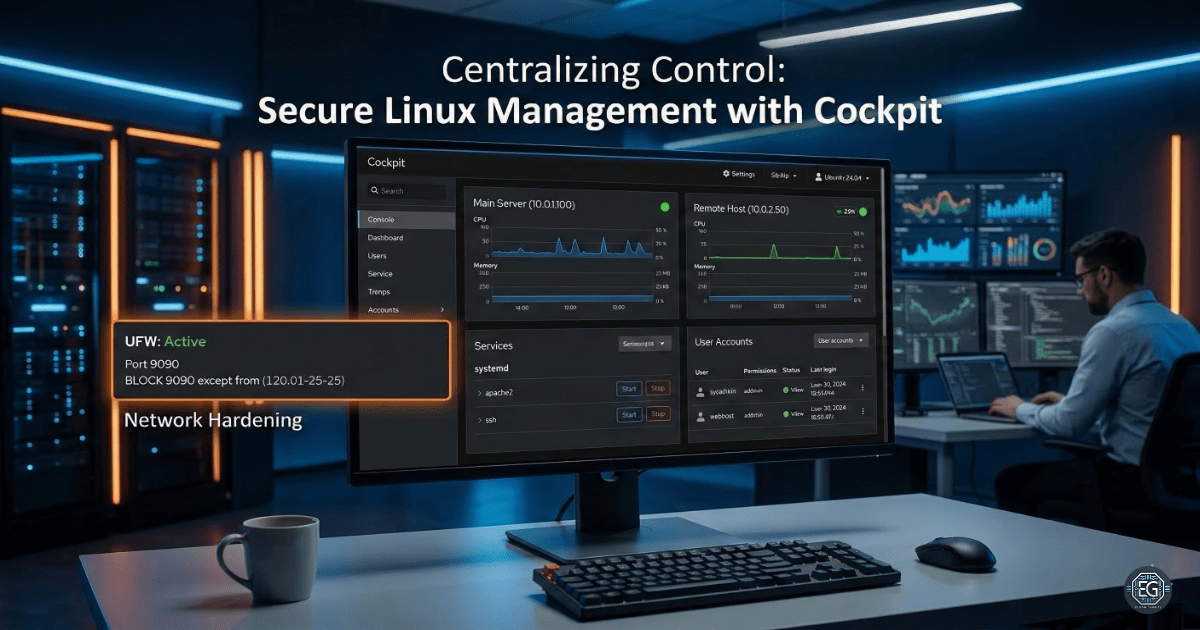
Using Cockpit to manage and secure multiple Linux systems from a single web interface.
REPORT – Webmin Secure Administration (Dual-Homed) – v1.1.0
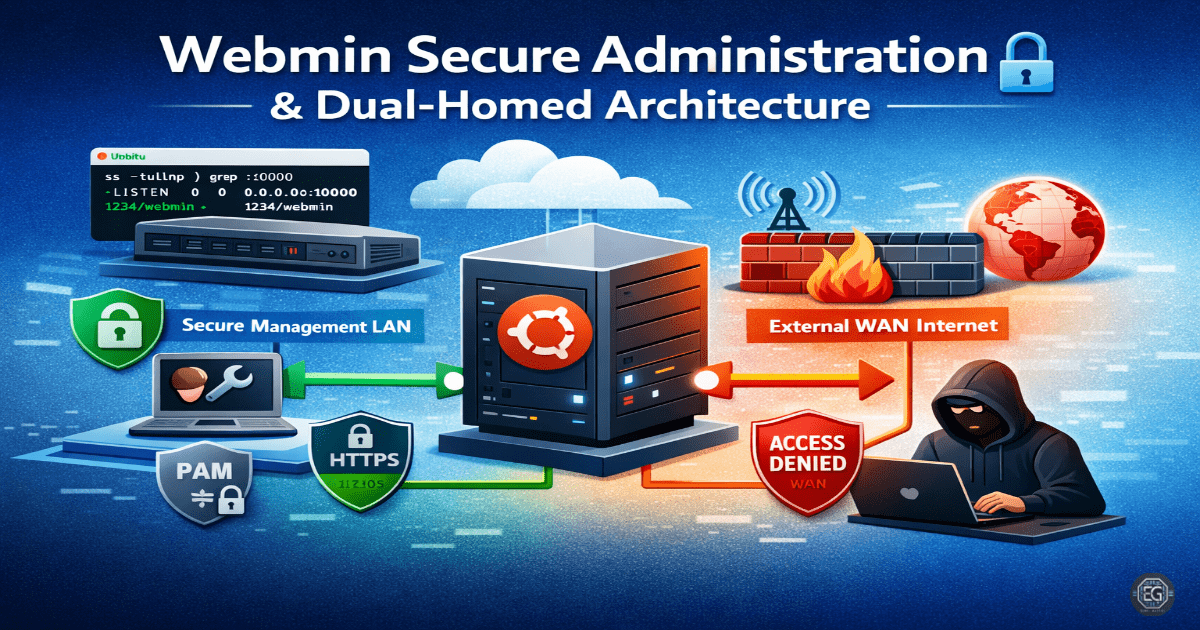
Securing a dual-homed Webmin administration server through PAM-based authentication, interface mapping, and IP-based firewall hardening.
REPORT – WinRM Secure Configuration and Validation – v1.0.0

Implementation and validation of secure Windows Remote Management (WinRM) protocols to ensure encrypted administrative communication and prevent unauthorized access.
REPORT – SMB Hardening for Credential Theft Protection – v1.0.0
Implementation of SMB signing, protocol deprecation, and session limits to protect against credential theft and relay attacks.
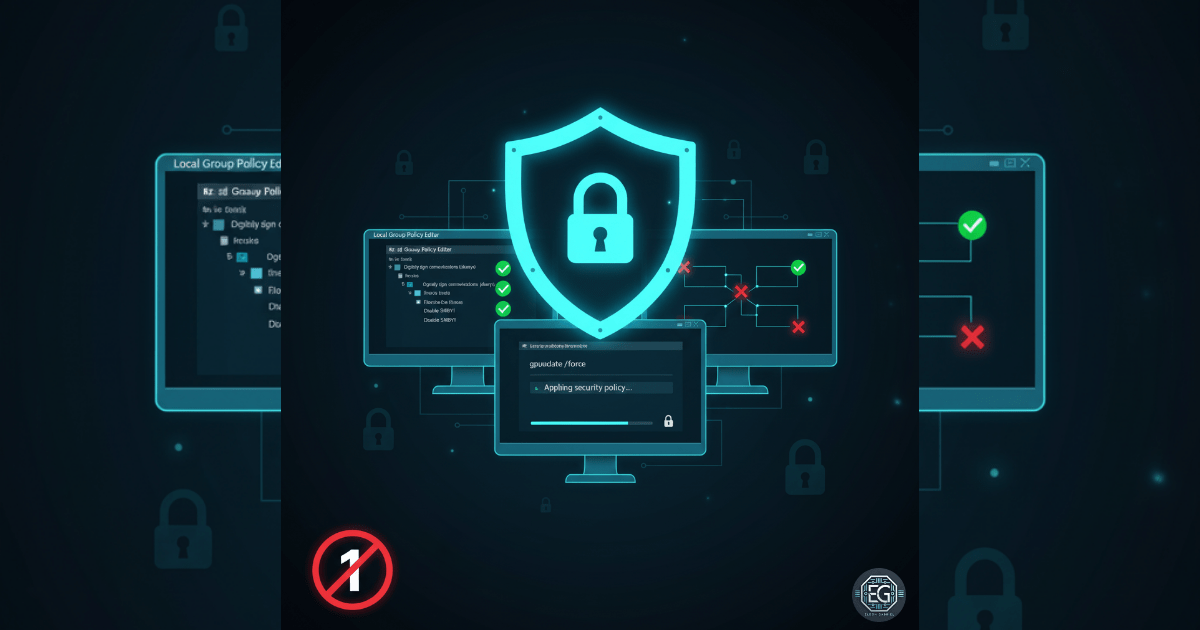
SOP – Hardening Windows Defender Using Local GPO – v1.0.1

Implementation of an immutable endpoint security baseline using Local Group Policy to harden Windows Defender against unauthorized modification and malware.
SOP – Anonymous Access Restriction & Recon Hardening – v1.0.2
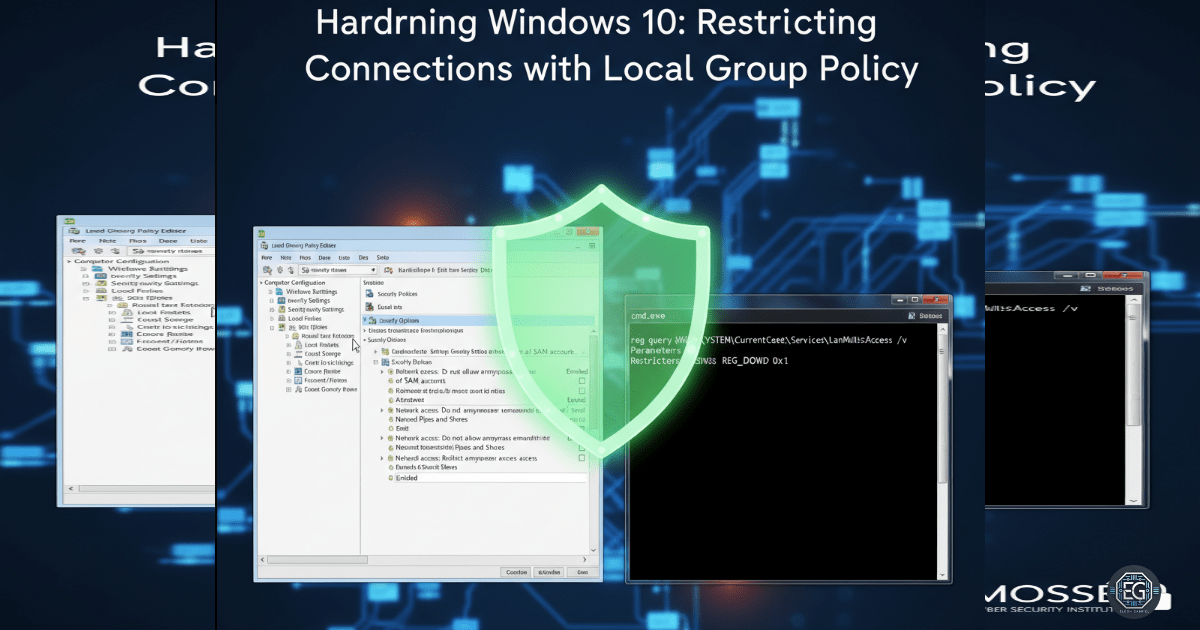
Implementation of Local Group Policy restrictions to prevent anonymous enumeration and null session reconnaissance against Windows endpoints.
REPORT – OS Patching Enforcement via Local GPO – v1.0.0
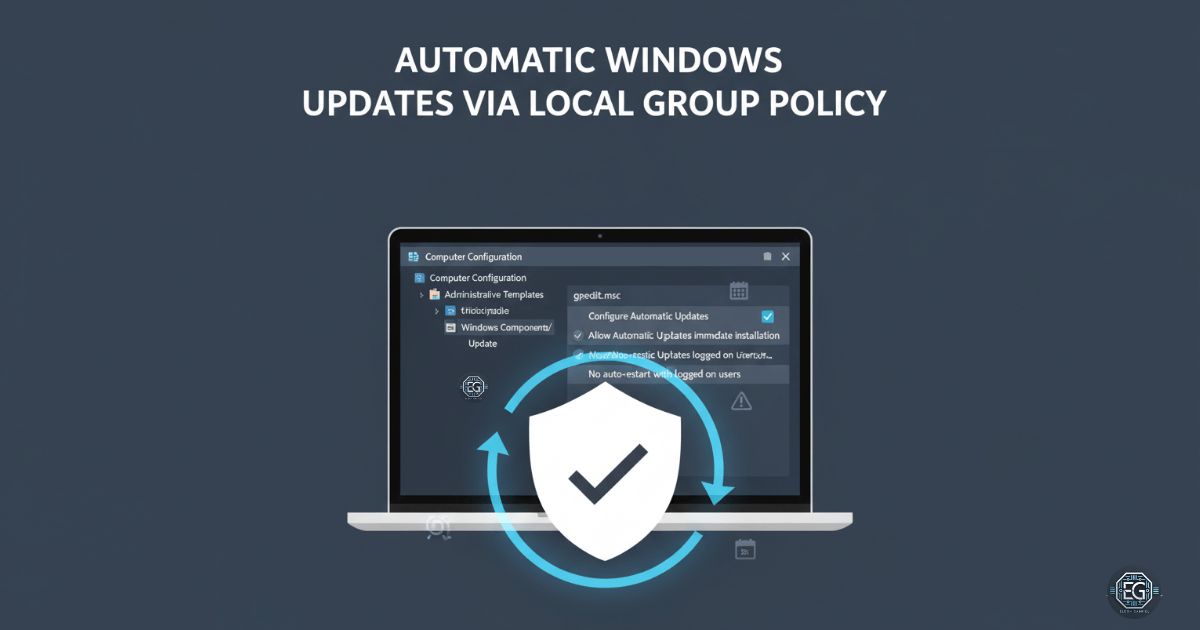
Implementation of automated operating system patching policies via Local Group Policy to balance system security with operational availability.
REPORT – Hardening Microsoft Edge via Local GPO – v1.0.0
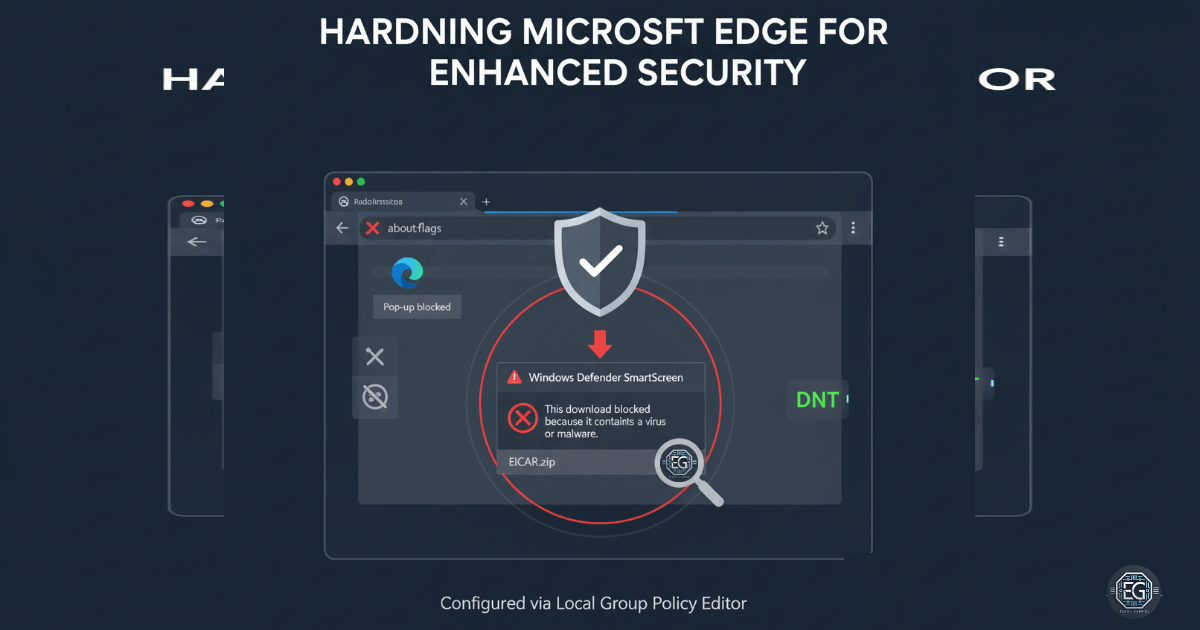
Implementation of security-focused Group Policy configurations to harden Microsoft Edge against web-based threats, unauthorized extensions, and data exfiltration.
REPORT – Deploy Controlled Folder Access via Local GPO – v1.0.0
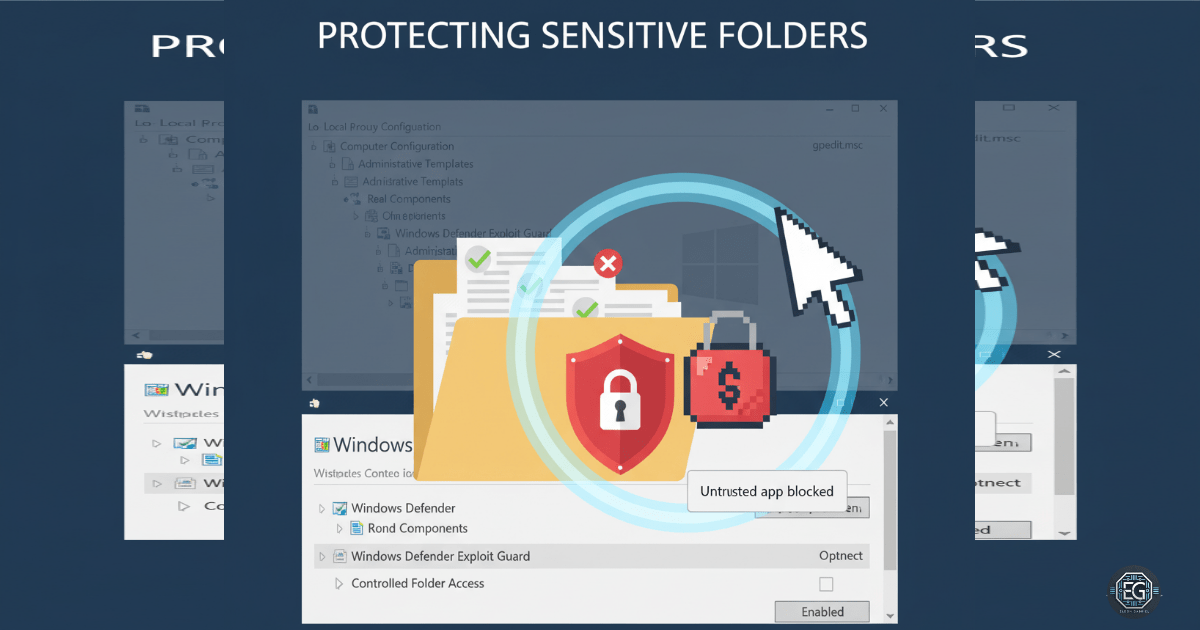
Implementation of Windows Defender Controlled Folder Access via Local Group Policy to mitigate unauthorized filesystem modifications and ransomware risks.
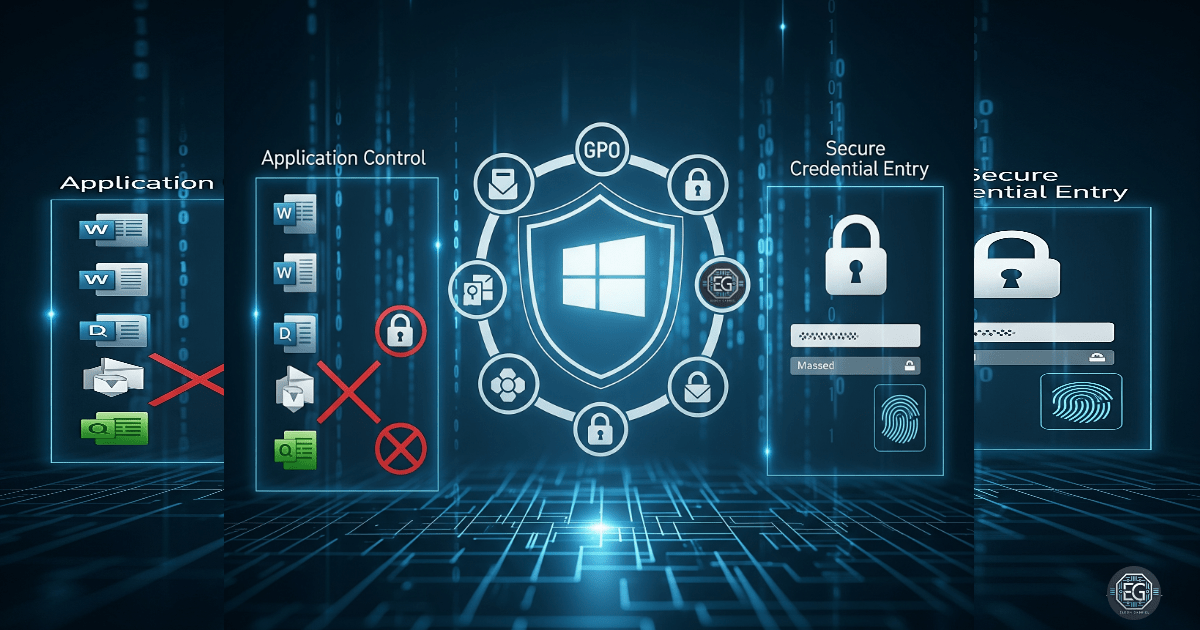
REPORT – GPO Hardening for Windows Application Control – v1.0.0
Implementation of Group Policy restrictions to prevent unauthorized software installation and harden Windows endpoints against malicious downloads.
REPORT – Monitoring Windows Processes with Procmon – v1.0.1
Utilization of Process Monitor (Procmon) to capture, filter, and analyze real-time system events for security auditing and process behavior validation.
REPORT – Endpoint Security with Windows Registry – v1.0.0

Implementation of registry-level restrictions to disallow unauthorized executable runs and harden the Windows OS against common user-mode threats.
Identity Security
REPORT – AD Disaster Recovery & Identity Restoration – v1.0.2
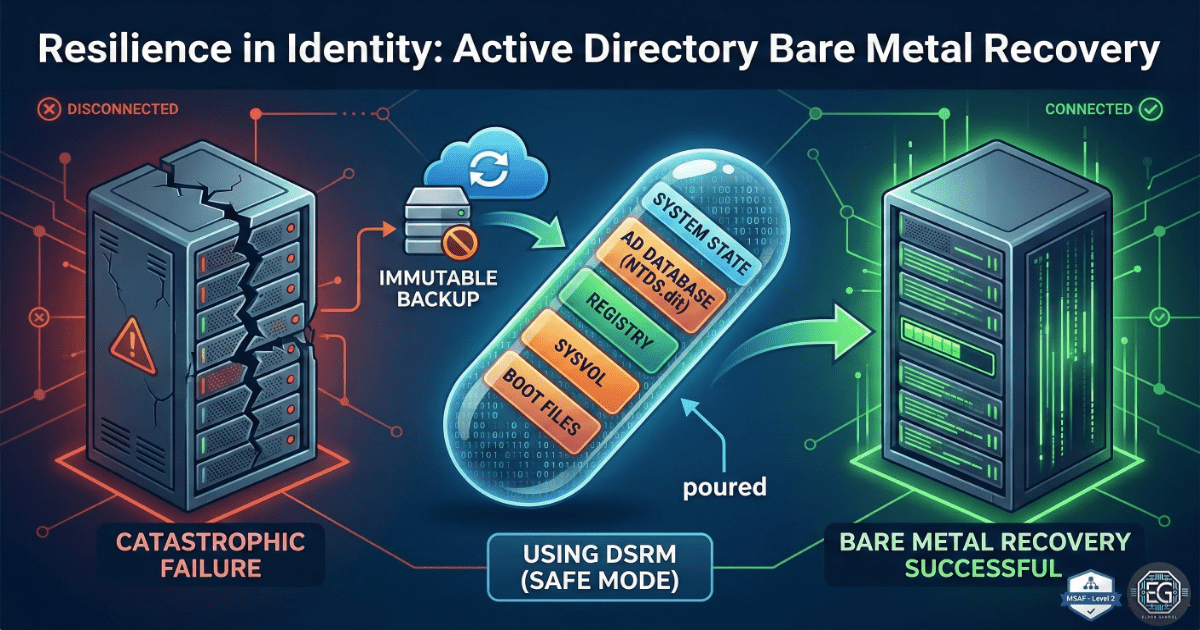
Successful restoration of an Active Directory environment using Bare-Metal Recovery (BMR) and System State restoration on Windows Server 2016.
REPORT – Hardening Windows User Rights via Local Group Policy – v1.0.0
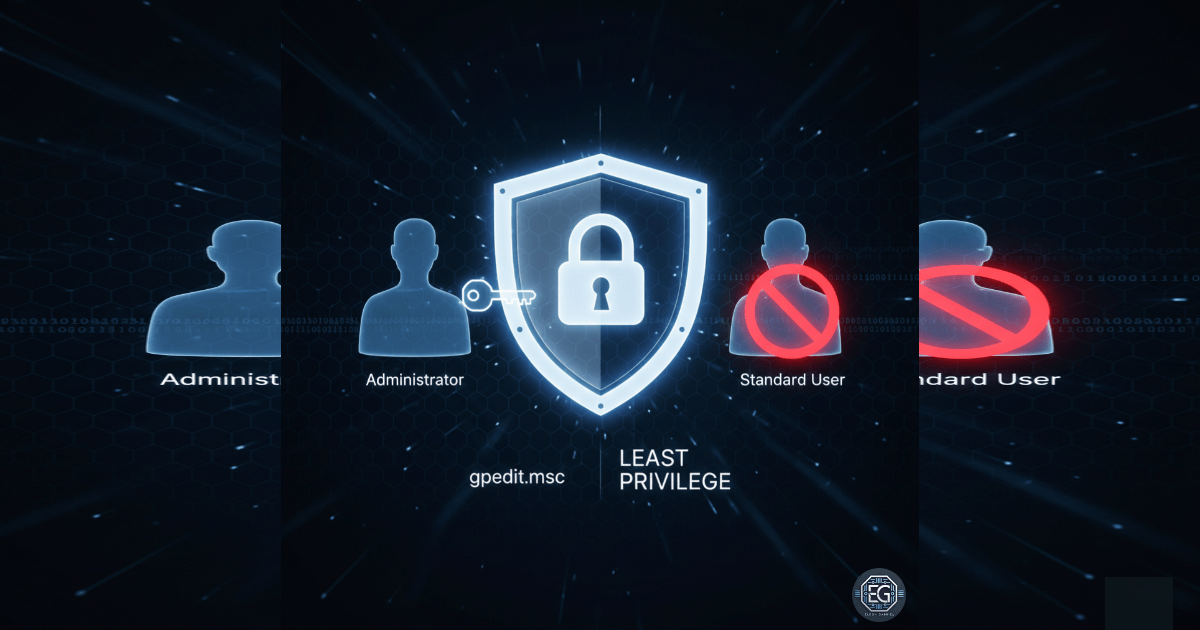
Configured User Rights Assignment policies via Local Group Policy to enforce least privilege and secure Windows endpoints.
REPORT – Applying a Local GPO for Session Lock Enforcement – v1.0.0

Configured Local Group Policy to enforce automatic session locks, improving Windows endpoint security.
REPORT – Deploy Local GPO for Windows Security Policies – v1.0.0

Implementation of a comprehensive security baseline using Local Group Policy to harden Windows endpoints against common network and system-level exploits.
SOP – Password & Account Lockout GPO Hardening – v1.0.1
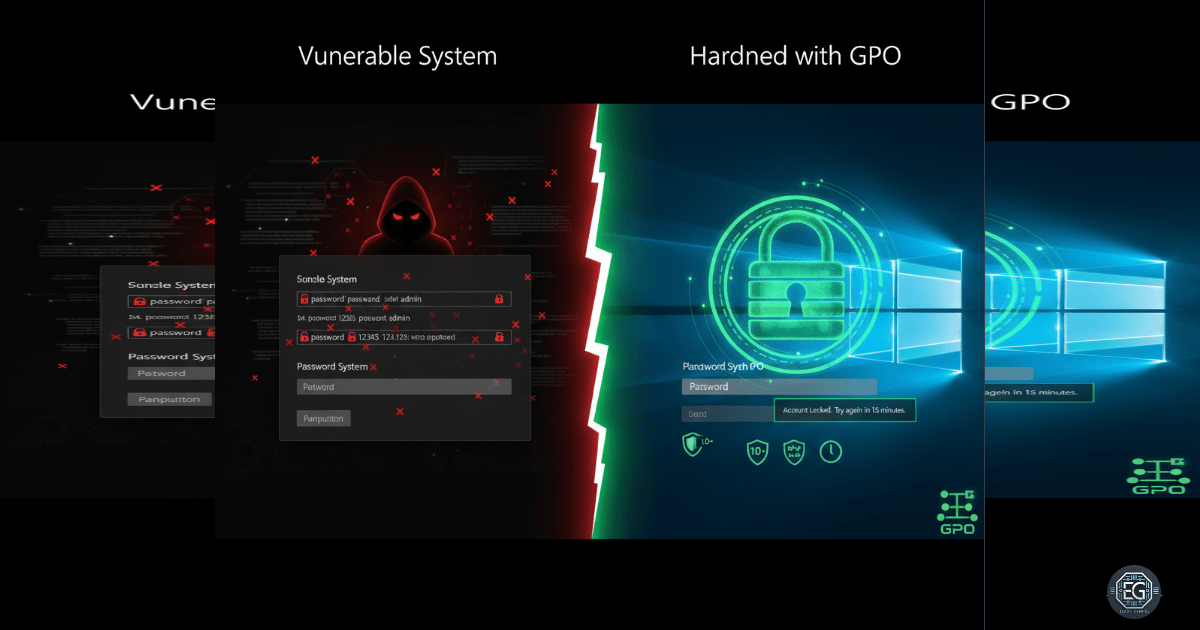
Implementation of mandatory password complexity and account lockout policies via Local Group Policy to defend against brute-force attacks and credential compromise.
REPORT – Harden UAC via Local Group Policy – v1.0.0
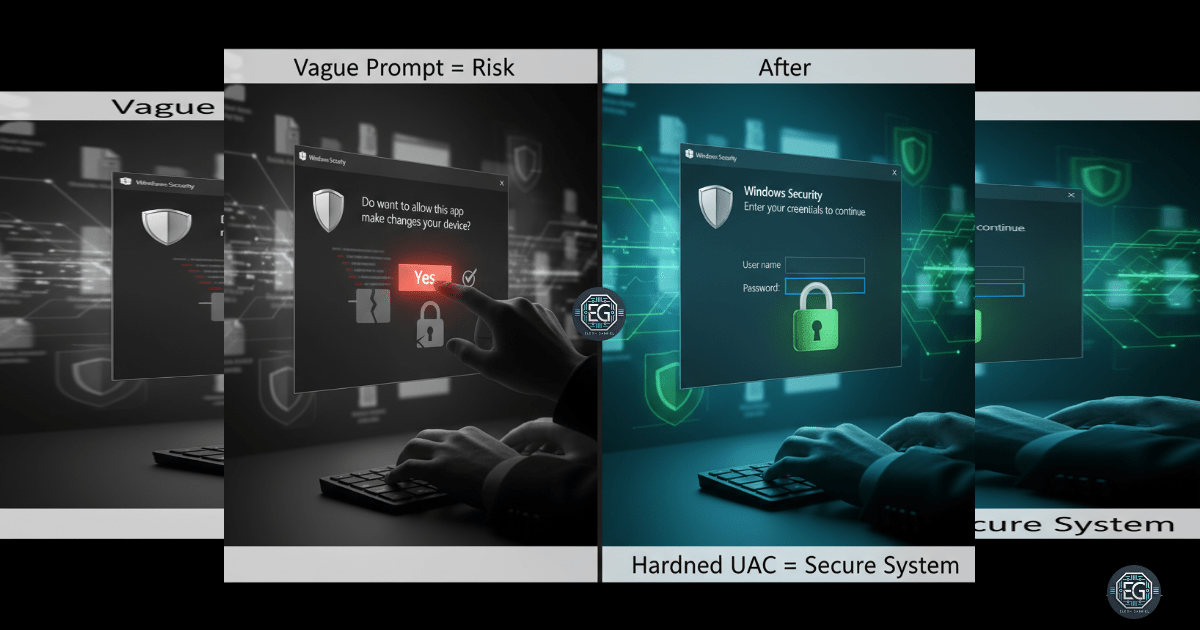
Implementation of hardened User Account Control (UAC) settings via Local Group Policy to mitigate unauthorized privilege escalation and credential spoofing.
REPORT – Hardening Credential Entry Using Group Policy – v1.0.0
Implementation of Secure Desktop and logon restrictions via Local Group Policy to reduce the risk of credential theft and keylogging attacks.
REPORT – Password Managers – v1.0.0
Implementation of structured password management strategies to improve credential hygiene and reduce the risk of account compromise.
REPORT – File Ownership Recovery – v1.0.0
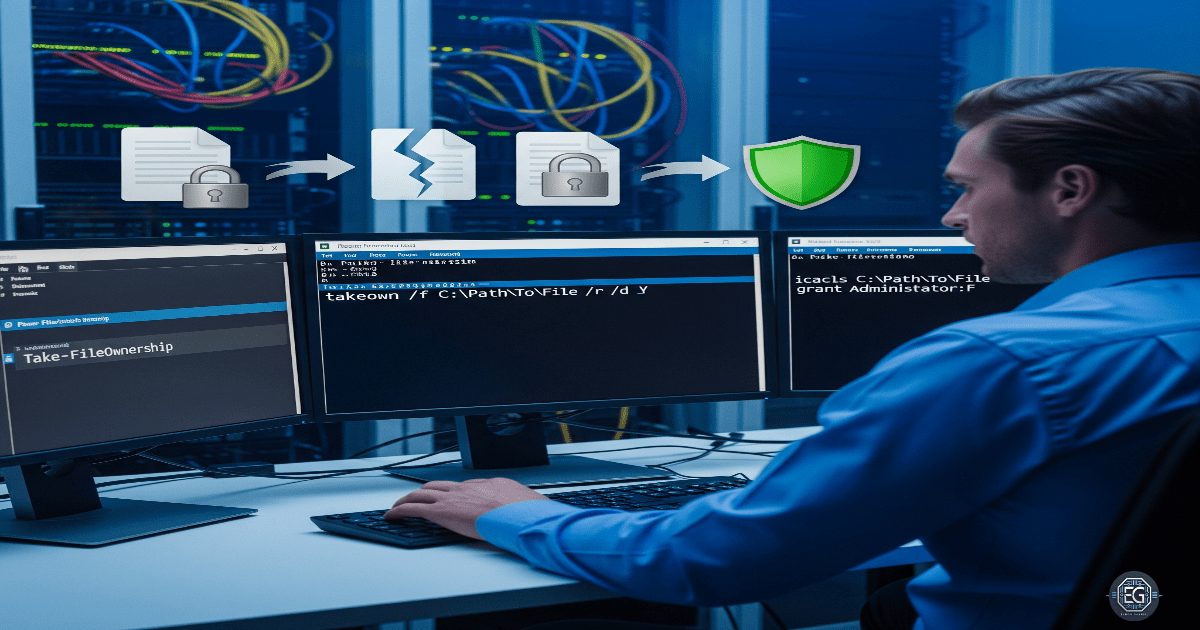
Investigation into Windows file ownership recovery methods, confirming NTFS as the authoritative source over the Registry for permission management.
Infrastructure and Systems
REPORT – Enterprise Hybrid-Cloud Migration – v1.2.0
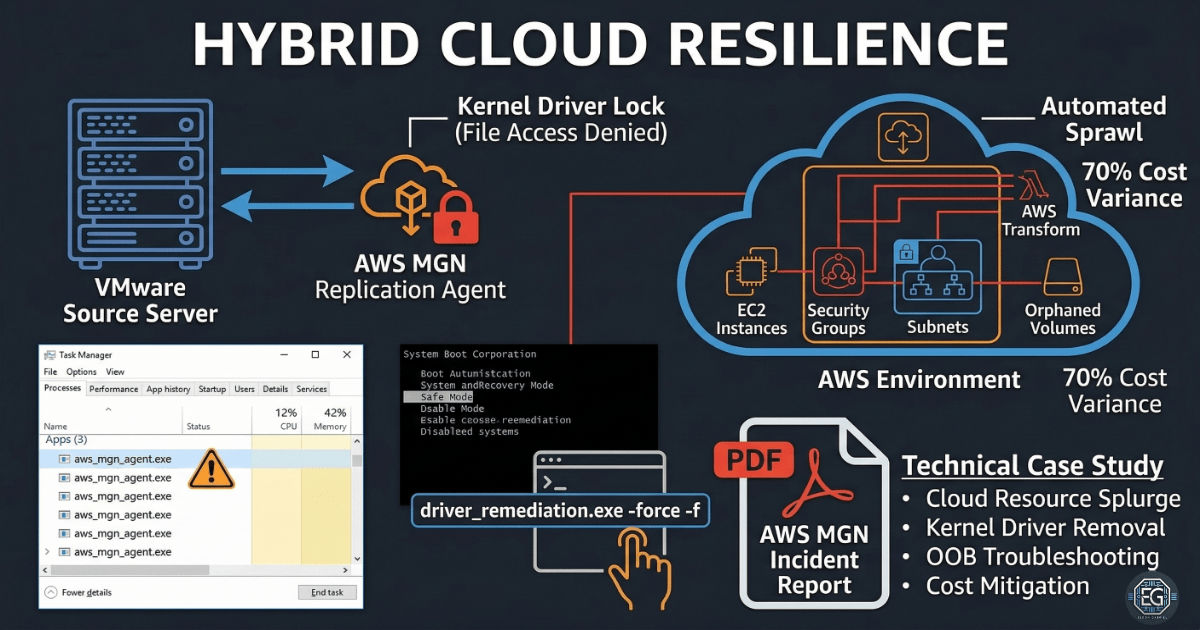
A practical troubleshooting case study on migrating VMware virtual machines to AWS EC2 and resolving kernel driver removal issues from the AWS Application Migration Service.
GUIDE – vSphere 8 Nested Lab on AMD Ryzen 6000 – v1.0.0
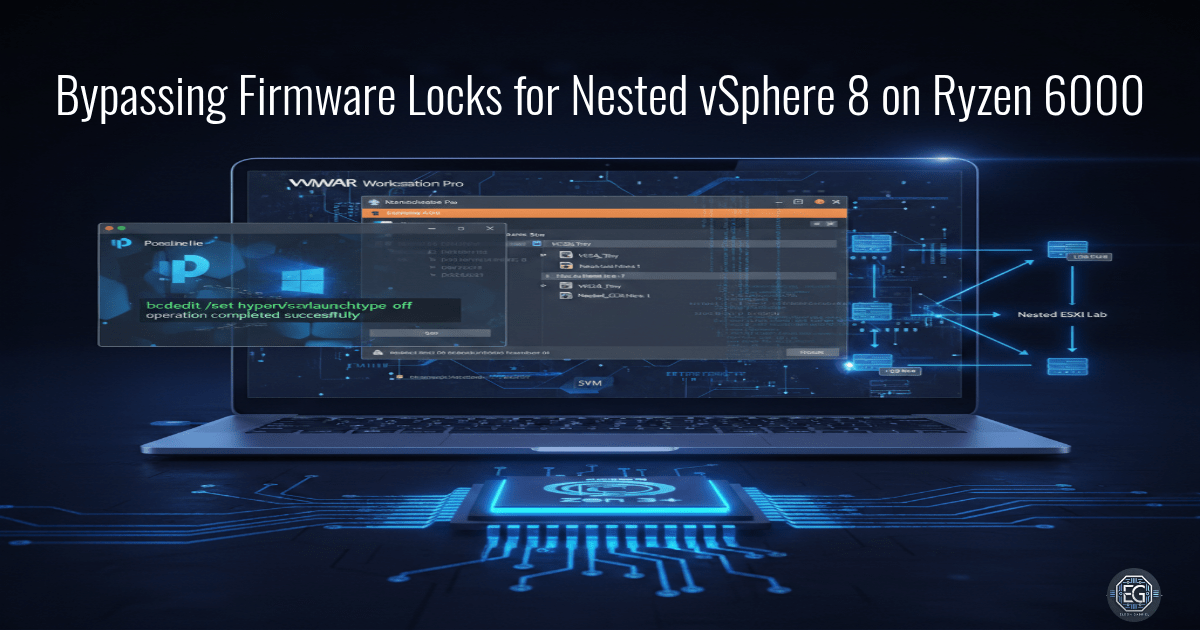
A technical deep-dive into enabling nested virtualization on restricted AMD mobile platforms by bypassing OEM firmware locks and Windows 11 VBS.
REPORT – SAR Performance Monitoring on Ubuntu – v1.0.1
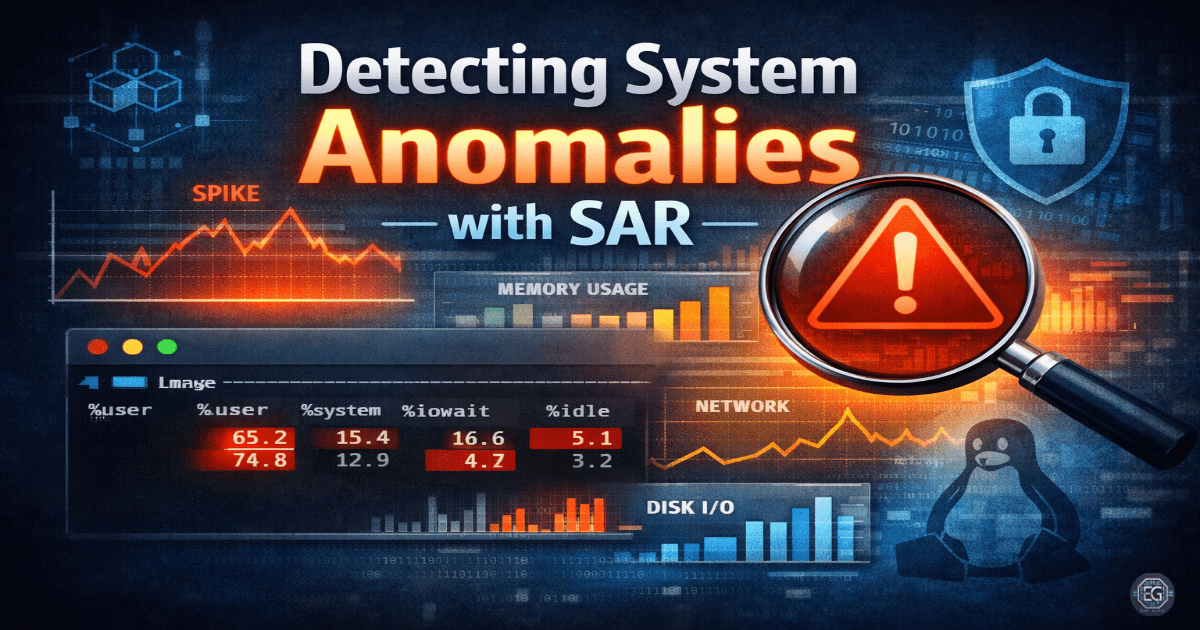
Implementation and analysis of system performance monitoring on Ubuntu using the System Activity Reporter (SAR) to identify resource bottlenecks and abnormal activity.
GUIDE – UTM Kali Linux Shared Folder Configuration – v1.0.0
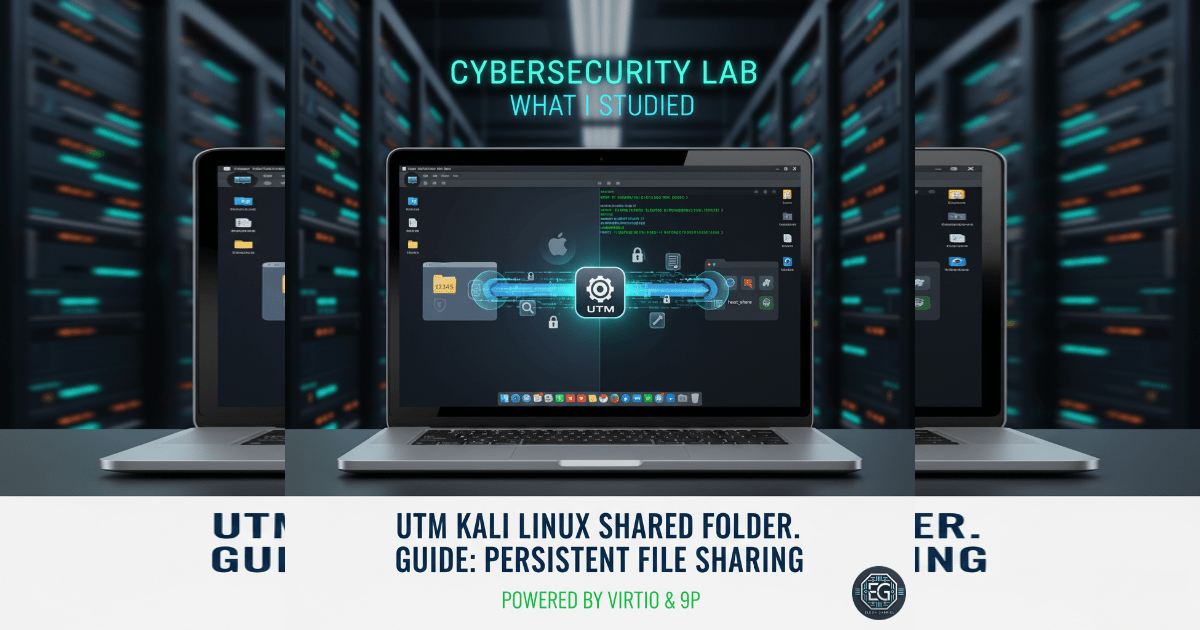
Implementation of a persistent shared folder between macOS and Kali Linux using the 9p protocol within the UTM hypervisor.
REPORT – GPO Hardening for Windows Application Control – v1.0.0
Implementation of Group Policy restrictions to prevent unauthorized software installation and harden Windows endpoints against malicious downloads.
Mastering GCP: Windows 10 VM Deployment
An independent lab demonstrating deployment of a Windows 10 virtual machine on Google Cloud Platform, showcasing cloud virtualization, secure configuration, and system administration skills.
Mastering Windows System Administration: 11 Independent Labs
A collection of 11 hands-on labs designed to build Windows administration skills, covering maintenance, troubleshooting, security, and automation — all tested in an AWS-hosted Windows 10 VM.
Networking
REPORT – pfSense APIPA Failure – v1.0.0
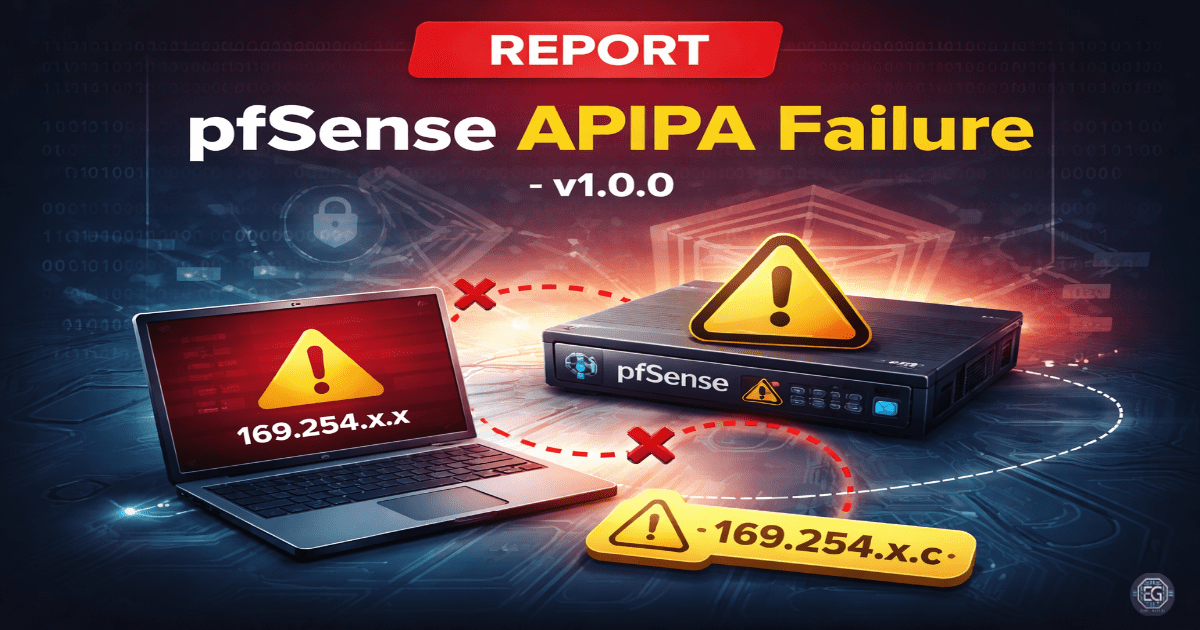
Loss of pfSense WebGUI access caused by APIPA addressing on the client system, resolved through static IP reconfiguration and connectivity validation.
REPORT – Access Control Bypass & Network Stability – v1.0.0
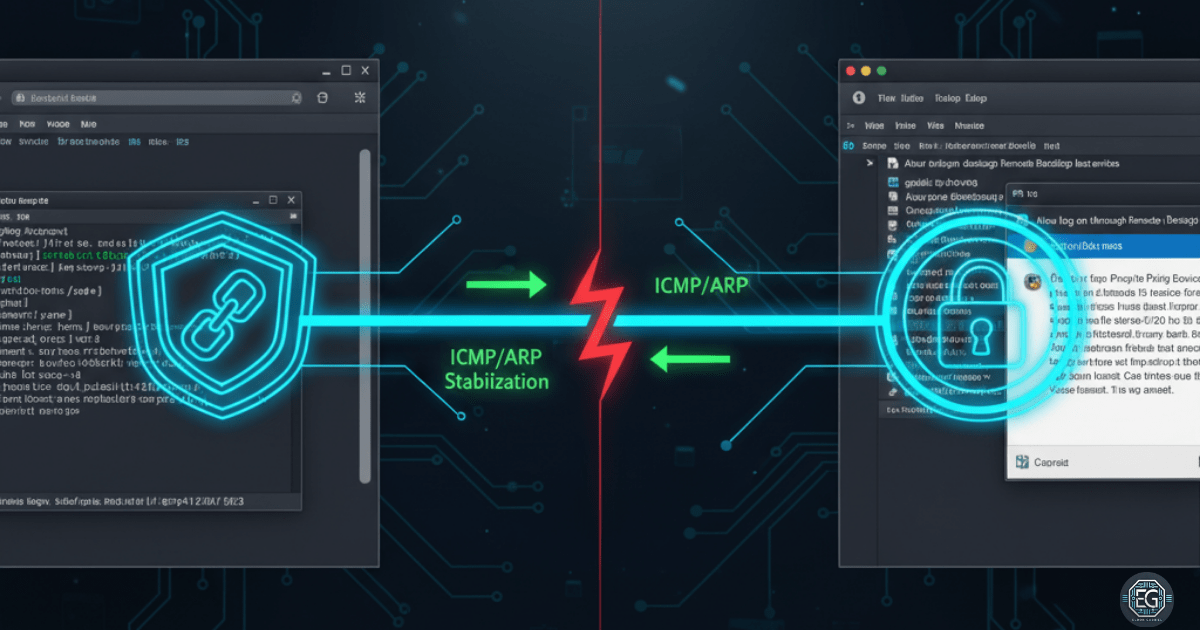
Resolution of a multi-layered connection failure involving Domain GPO restrictions and virtual network instability in a macOS-UTM environment.
REPORT – RDP Troubleshooting for AWS Users – v1.0.0
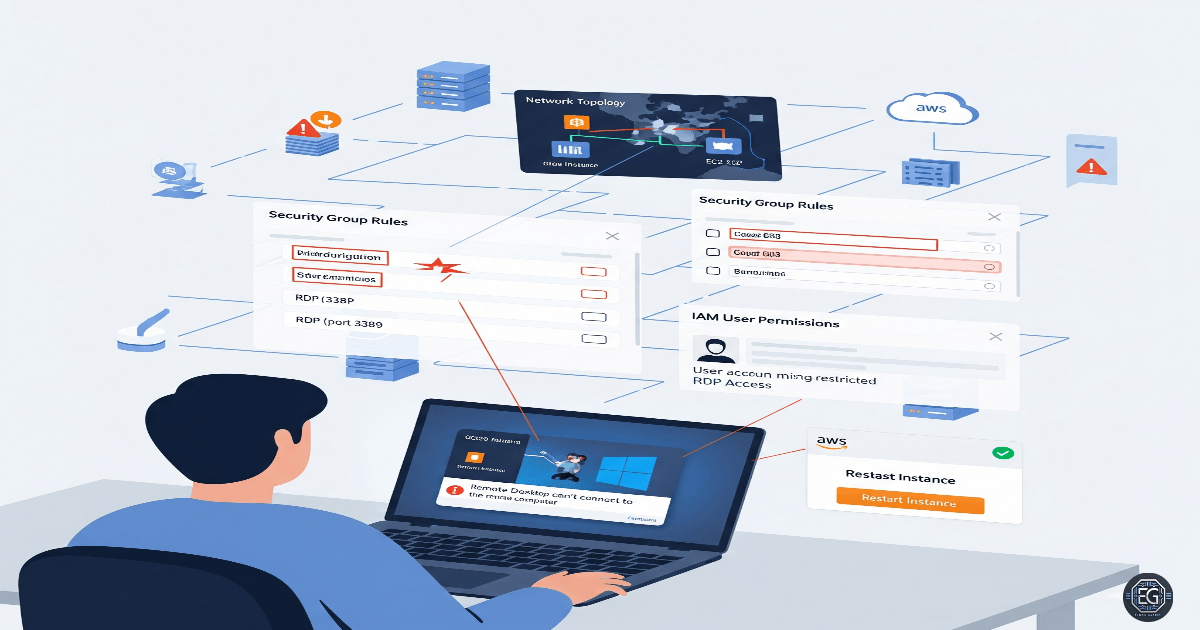
Resolution of Remote Desktop Protocol (RDP) access failures on an AWS-hosted Windows instance through group membership and policy validation.
REPORT – IP Subnetting Fundamentals – v1.0.0
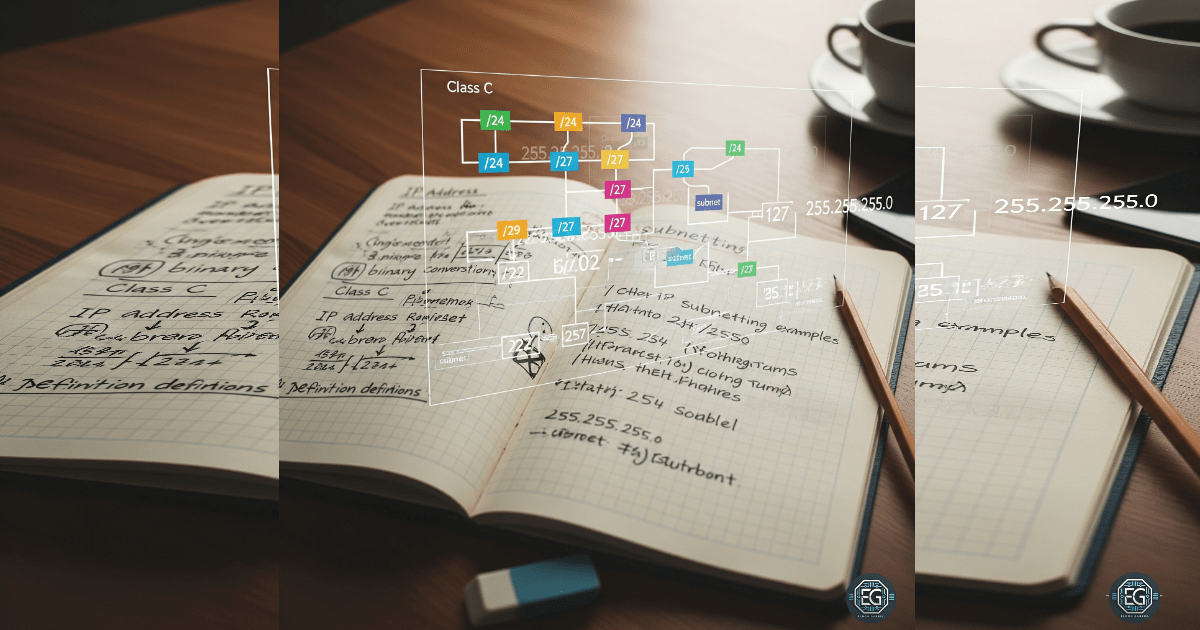
Implementation of structured IP subnetting to enable network segmentation, reducing the attack surface and improving access control.
OSINT Investigation
REPORT – Geolocation and Image Verification Analysis – v1.0.0
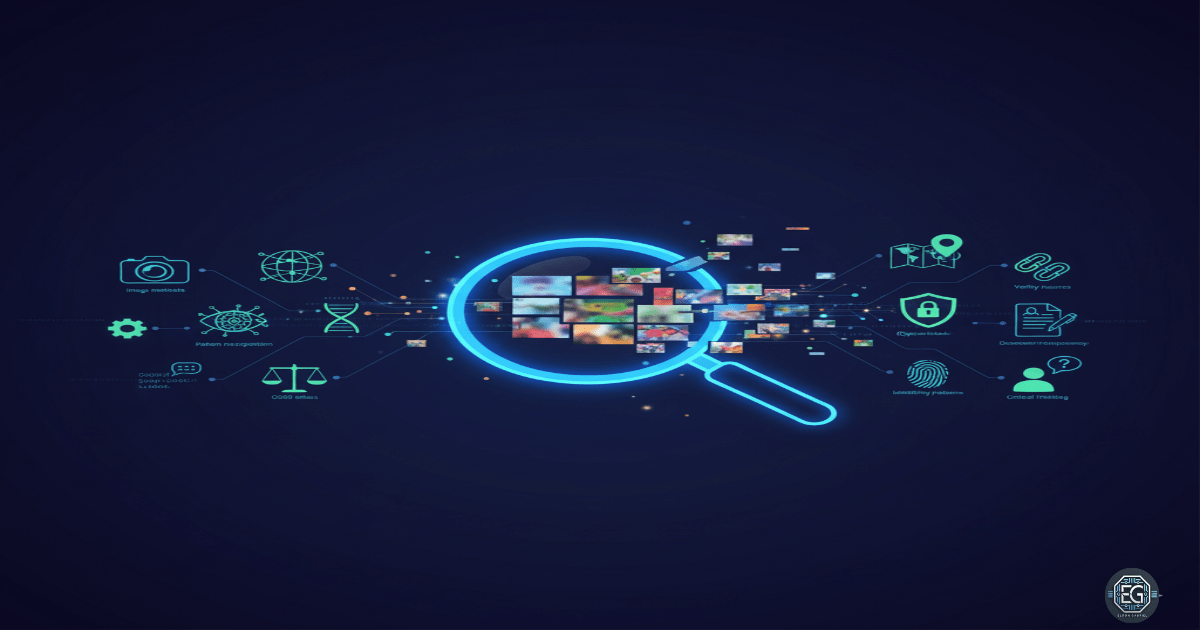
Application of advanced reverse image search and visual analysis techniques to verify artifacts and geolocate global landmarks.
REPORT – OSINT Email Enumeration & Validation – v1.0.1
Execution of email reconnaissance and validation techniques to identify organizational naming conventions and verify active communication channels.
REPORT – Using Google Translate for OSINT – v1.1.0
Using translation tools to process and validate foreign-language data from multiple sources including articles, code, images, documents, and webpages.
Governance and Risk
SOP - Access Control Incident & NIST Alignment - v1.2.1
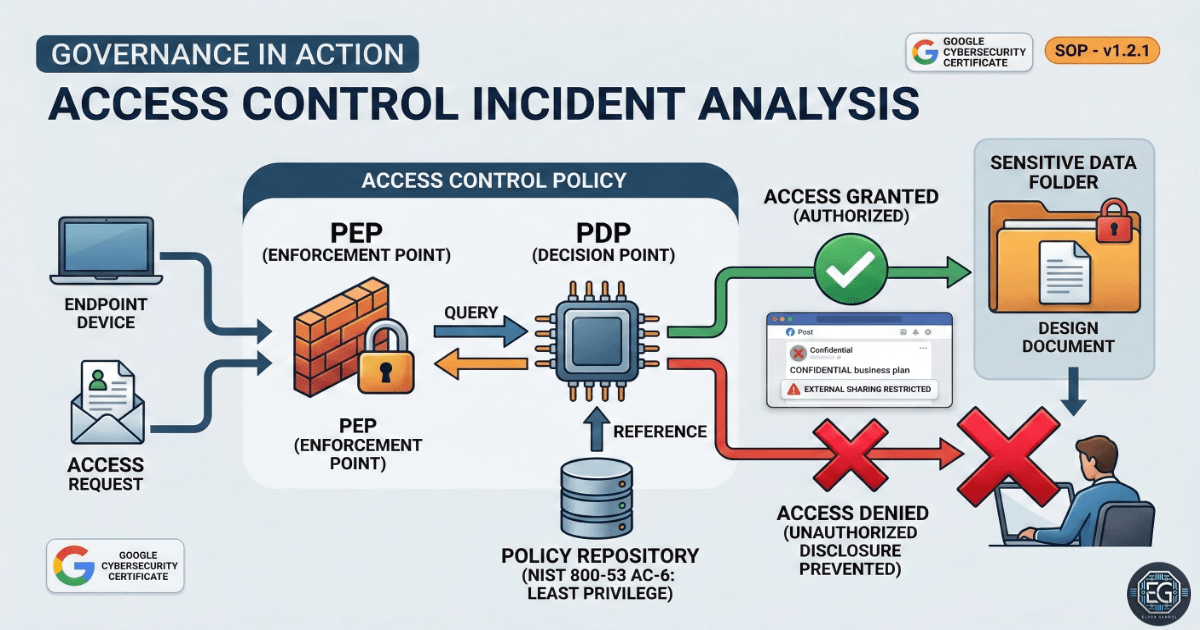
Analysis of a data exposure incident caused by weak access controls and lack of enforced security policies.
Operational Approach
REPORT – Prompt & Rubric Evaluation Exercises – v1.0.0
Analysis of prompts and rubrics to improve clarity, reduce ambiguity, and increase consistency in technical evaluations.
Operational Resilience
GUIDE – Backup and Restore Using Duplicati CLI – v1.0.1
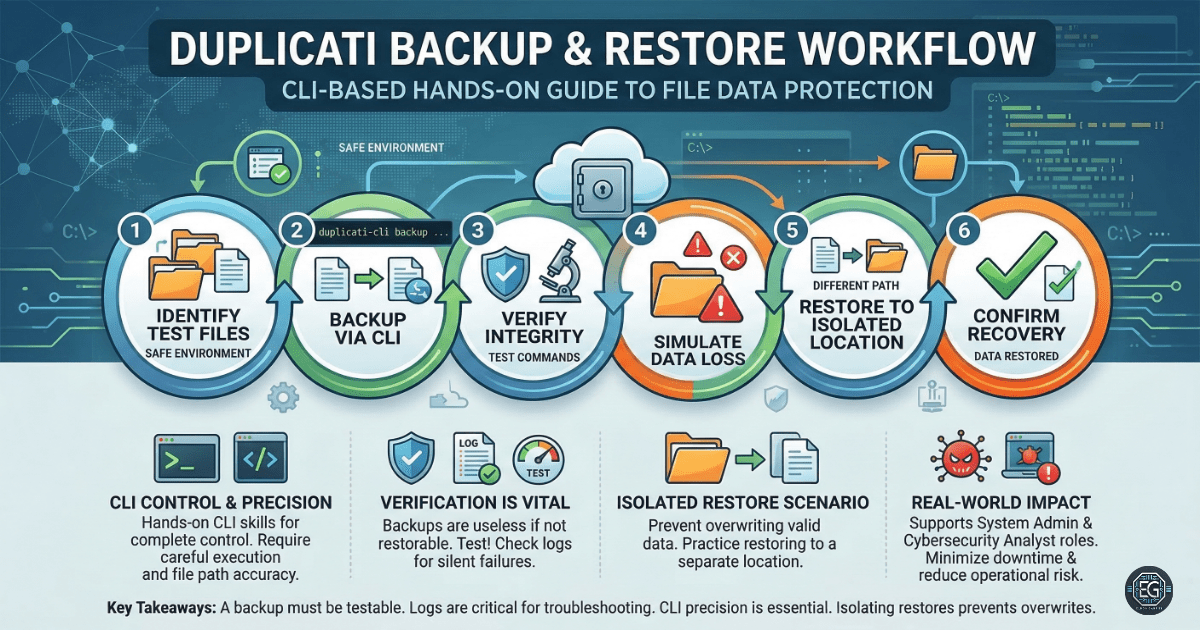
Execution and validation of command-line based backup and recovery workflows using Duplicati to ensure data recoverability and integrity.
