Introduction
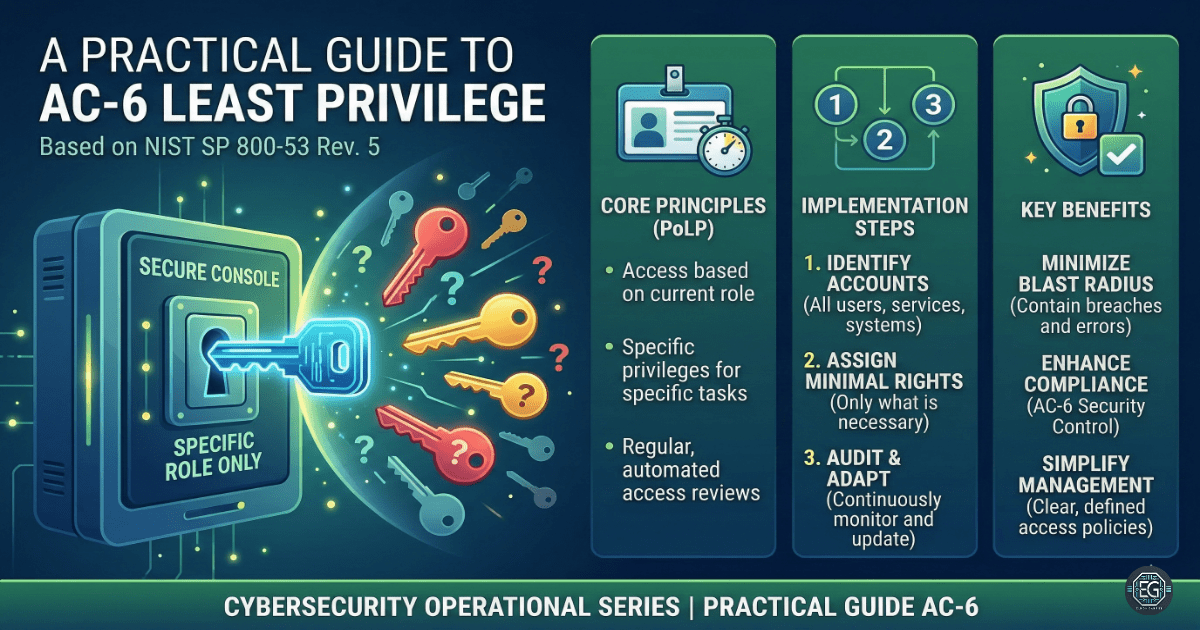
This exercise focused on applying the principle of least privilege based on NIST SP 800-53 AC-6. The goal is to understand how limiting access reduces security risks and protects systems from misuse.
What I Studied
- Least Privilege (PoLP): giving users only the access they need
- Role-Based Access Control (RBAC): assigning permissions based on job roles
- Separation of Duties: splitting critical tasks between multiple users
- Privileged Account Management: limiting and securing admin-level access
- Access Reviews: checking and removing unnecessary permissions
- Logging and Monitoring: tracking access activity for suspicious behavior
- Just-In-Time (JIT) Access: granting temporary access when needed
The exercise followed a structured approach to control access and reduce risk across systems.
What I Learned
- Excessive access is one of the biggest security risks in any system.
- Users often have more permissions than they actually need.
- Limiting administrative accounts reduces the risk of system-wide compromise.
- Monitoring access is as important as controlling it.
I also learned that access control is not a one-time setup. It requires regular review and adjustment to remain effective.
Why It Matters
Least privilege is a core part of system security. If attackers gain access to an account with high privileges, they can move quickly through systems and cause major damage.
In real environments, this is similar to giving employees keys to every room in a building. If one key is stolen, everything is exposed.
This approach helps organizations:
- Reduce attack surface
- Prevent unauthorized access
- Detect suspicious activity earlier
- Meet compliance requirements
- Reflection & Next Steps
GUIDE – Security Control Standard_ AC-6 Least Privilege (NIST SP 800-53) – v1.0.2
Reflection & Next Steps
TThis exercise improved my understanding of access control and risk reduction. I will continue to apply the principle of least privilege in system configurations and explore more advanced access control models.