Governance in Action: Access Control Incident Analysis
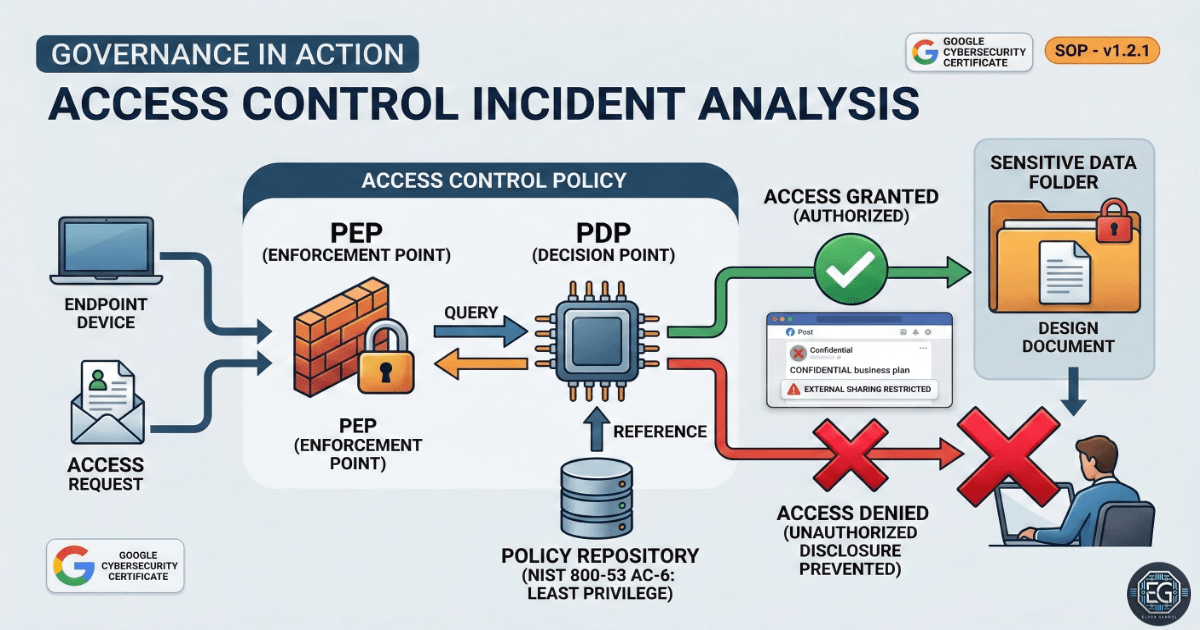
When a data leak occurs, people often blame a person. However, in security, leaks are usually not just human mistakes. They happen because security controls are weak or missing.
In this project, I analyzed a real-world data leak to understand how a simple mistake turned into a serious risk. The main issue was the lack of strong technical controls to stop the mistake from spreading.
What I Studied
- Reviewed a data leak where confidential business plans were shared by mistake
- Module: Google Cybersecurity Professional Certificate – Assets, Threats, and Vulnerabilities
- Used Data Risk Assessment, Root Cause Analysis (RCA), and Control Gap Analysis
- Applied the Principle of Least Privilege (POLP)
- Compared technical controls vs manual processes
What I Learned
- Identified gaps between trust-based and enforced security
- Learned that relying on users to manage access manually increases risk
- Saw how excessive access leads to data exposure
- Practiced explaining why technical controls are stronger than verbal policies
Why It Matters
Data is one of the most valuable assets in any organization. If it is exposed, it can lead to financial loss, legal issues, and damage to reputation.
Access control should not rely on trust. Like a hotel key card, systems should only allow access to what a user is permitted to enter. Anything else creates risk.
How It Maps to the Job / Framework
-
NIST NICE – Cyber Defense Analyst: Builds skills in analyzing system activity and identifying security risks
-
ASD Cyber Skills Framework – Governance and Risk: Focuses on risk assessment and applying proper security controls
Key Takeaways
- The Principle of Least Privilege must be enforced by the system
- Default settings should always be reviewed and secured
- Systems must account for human error
- Strong access control requires both policy and technical enforcement
Related Projects
SOP – Access Control Incident & NIST Alignment – v1.2.1
Technical Skills Demonstrated
- Access control analysis
- Root Cause Analysis (RCA)
- Risk assessment and control gap identification
- NIST framework mapping
- Security policy evaluation
Conclusion
This project showed that data leaks are often caused by weak system controls, not just human mistakes. By applying proper access restrictions and enforcing security policies, organizations can reduce risk and protect sensitive information.
It also reinforced that security must be built into the system, not left to user behavior alone.